IT Pro Verdict
The Firebox M440 is a versatile security appliance that beats the competition soundly on value. Security features are excellent and our lab tests confirm it delivers on WatchGuard’s performance promises.
Pros
- +
Superb value; Top performance; Extensive security measures, High port density, Integral wireless gateway controller
Cons
- -
Proxy setup takes practice
With its fire-engine red chassis you can't miss a WatchGuard security appliance but the Firebox M440 is an eye-catcher for a number of other good reasons. It's designed to help big businesses enforce custom security policies across multiple network segments but without complicating the process.
This 1U rack appliance is stuffed with ports as it offers 25 copper Gigabit and two 10-GbE SFP+ ports. For a sub-10K appliance, it's a powerful beast as well with WatchGuard claiming a top 6.7Gbits/sec firewall throughput and 1.6Gbits/sec for UTM.
It's excellent value, too. A three-year LiveSecurity subscription activates the firewall, VPNs, HTTPS inspection plus full customer support and has an RRP of 4,942 ex VAT.
An NGFW subscription adds IPS and application controls and takes the total price to 6,798 while WatchGuard's Security Suite pushes the total to 8,449 and activates web content filtering, anti-spam, gateway anti-virus and WatchGuard's reputation enabled defence. You can also add WatchGuard's optional advanced persistent threat (APT) blocker and data leak prevention (DLP) services.
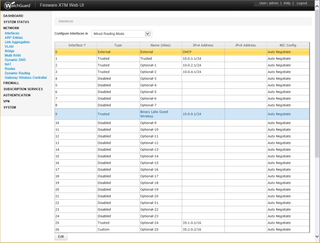
The appliances' ports are easily configured and can have custom security policies applied to them
WatchGuard's port-fest
We found the M440 very easy to deploy. The tidy web interface runs a wizard to secure the appliance and get basic Internet access running on an external port along with DHCP services on your first trusted interface.
The M440 supports three operational modes and we recommend the mixed routing mode - it's the most flexible as it allows all ports to be defined as separate interfaces. Configuring the remaining ports is a cinch as we defined them as external, trusted, optional or custom and added DHCP services on selected trusted ports.
It's worth giving each port an alias as it makes it easier to assign firewall policies. Along with choosing which traffic to control, you assign policies to source and destination ports which could, for example, be all trusted and external ports or just specific ones.

The HTTP proxy is used to apply web filtering actions and WatchGuard provides 130 URL categories
Proxy practice
The M440 uses proxies for all security services where we created firewall rules for each one defining the interfaces they applied to and their actions. There are plenty to choose as you have proxies for HTTP, HTTPS, FTP, SIP, H.323, POP3 and SMTP.
We recommend practicing proxy configuration as it can initially be a bit of a fiddle to get them working. First, you view the predefined actions for each proxy and clone them for use in your own policies.
To apply web filtering, we cloned the HTTP Client action and tweaked functions such as web caching, deny messages, alerting and so on. Next, we selected the WebBlocker subscription service and created a filtering action for it by choosing from 130 Websense categories to block or allow.
Now we could link our WebBlocker action with the policy, activate it with a firewall rule and choose which source and destination ports it should apply to. It sounds complicated but it gets easier with time and we could create a wide range of web filtering policies and apply them to different network segments.
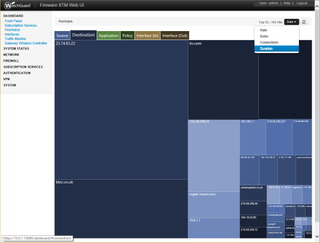
The built-in FireWatch app provides a handy graphical chart showing the top activities on your network
More proxy action
For anti-spam, we cloned a POP3 client action from the spamBlocker service and configured it to tag messages classed as spam', suspect' and bulk'. Gateway anti-virus can be enabled on selected policies while APT scans incoming files and checks their MD5 hash with the LastLine cloud service to see if they're known malware.
The optional DLP service includes predefined sensors for HIPPA and PCI but we could easily create our own. DLP can be enabled on the HTTP, FTP and SMTP proxies where it checks for specific keywords and drops the connection while for email, it can strip keywords out or quarantine the entire message.
The M440 can function as a central wireless controller for WatchGuard's own APs and its central group of eight Gigabit ports are PoE enabled. Pairing a WatchGuard AP200 with the M440's wireless gateway controller allowed us to assign SSIDs to its 2.4GHz and 5GHz radios, enforce wireless security and apply separate proxy policies to the port it was connected it.
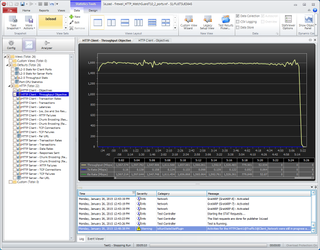
The lab's Ixia Xcellon-Ultra NP blades recorded a steady 1.6Gbits/sec HTTP throughput with UTM enabled
Ixia performance tests
To test real world performance, we used the lab's Ixia Xcellon Ultra-NP network load modules and configured the IxLoad control software to generate 512KB HTTP web pages. With the load modules connected to the M440's 10GbE ports and a basic HTTP firewall policy applied to them, we saw an average HTTP throughput of 3.5Gbits/sec.
With gateway AV scanning activated in the policy, throughput dropped to 2.4Gbits/sec slightly more than WatchGuard claims. With AV turned off and IPS enabled we recorded an average of 2Gbits/sec a little less than the quoted figure of 2.2Gbits/sec.
To test UTM performance we enabled both AV and IPS and saw throughput settle at a steady 1.6Gbits/sec thus confirming WatchGuard's own speeds. This is the maximum achievable as appliance CPU usage was maxed out at 100 per cent for all tests.
Conclusion
Along with a superb range of security features, the M440 looks top value as it costs significantly less than SonicWALL's E-Series NSA 6500. Its high port count makes it easy to enforce custom security policies on different network segments and its integral wireless gateway allows these to be applied just as easily to wireless clients.
Verdict
The Firebox M440 is a versatile security appliance that beats the competition soundly on value. Security features are excellent and our lab tests confirm it delivers on WatchGuard’s performance promises.
Chassis: 1U rack
Network: 25 x Gigabit, 2 x 10GbE SFP+ (PoE on ports 9-16)
Other ports: 2 x USB2, RJ-45 serial port
Power: Hot-plug 500W PSU, (optional redundant PSU)
Management: Web browser
Warranty: 1yr advanced hardware replacement
Options: 3-year subscriptions: APT, £2,979; DLP, £1,438 (all ex VAT)
Dave is an IT consultant and freelance journalist specialising in hands-on reviews of computer networking products covering all market sectors from small businesses to enterprises. Founder of Binary Testing Ltd – the UK’s premier independent network testing laboratory - Dave has over 45 years of experience in the IT industry.
Dave has produced many thousands of in-depth business networking product reviews from his lab which have been reproduced globally. Writing for ITPro and its sister title, PC Pro, he covers all areas of business IT infrastructure, including servers, storage, network security, data protection, cloud, infrastructure and services.



