RFID open to criminal abuse
From triggering bombs to faking passports, report exposes the flaws in this emerging technology.
Terrorists could potentially use RFID technology in electronic passports to set off a bomb when a particular target comes within reach, warns a leading electrical engineering expert.
Nigel Gilbert of the Royal Academy of Engineering suggests a number of ways in which RFID technology could be abused by both criminals and governments in his report entitled 'Dilemmas of Privacy and Surveillance: Challenges of Technological Change', published this week.
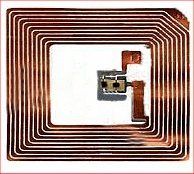
In particular he is concerned that that unencrypted data stored on an RFID chip in an e-passport, such as those currently being implemented by the UK Government, can be read by anybody passing near the document holder with the right equipment.
"Not only could a passport holder be revealing identifying and personal information to passport control, but they could also be unwittingly revealing their personal data to 'spies' who had equipped themselves with readers," says Gilbert in the report.
These eavesdroppers, he says, could use the resulting data for fraud of various kinds, for example stealing biometric details and accessing other services that use biometrics like pay-by-touch systems.
"With sensitive personal details readable over a distance, it could even become possible, with appropriate antennas and amplification, to construct a bomb that would only detonate in the presence of a particular nationality or even a particular individual," suggests Gilbert.
Clive Longbottom, an analyst with consultancy Quocirca, believes the terror risk is remote.
Get the ITPro. daily newsletter
Receive our latest news, industry updates, featured resources and more. Sign up today to receive our FREE report on AI cyber crime & security - newly updated for 2024.
"The possibility of using RFID in passports to set off a bomb is rather an outside chance, as the chip reader would need to be with a few centimetres of the person involved, as there is no active component to the passport," he told IT PRO.
The terrorists, he says, would also need to have hacked the passport database to gain the details of the passport signature, and then would have had to replicate the passport reader technology to fully recognise that signature: "If they can do that, then they probably don't need to be so clever in placing a bomb - why not just use standard blunt weapon approaches, or a sniper?"
Longbottom believes that RFID does, nevertheless, represent a serious security challenge, open to official or unofficial misuse.
"RFID can be misused, and doubtless will be by the powers that be," he says. "We can put in place safeguards for technological approaches. We can also use technology to stop wilful abuse - for example, creating the need for dual biometric security credentials to access certain information means that you have to have at least two people involved in the abuse. I don't think that RFID is the problem, it's far more down to how it's used."




