New software gives parents Big Brother access to kids phones
Watchdog software Radar enables parents to monitor activities on their child's mobile phone, as well as place protective restrictions on access and calls.
Mobile phones have become a key tool in helping people stay connected. However, in the hands of children the technology poses a potential privacy and safety risk and parents are now looking for a way to ensure their child's phone use doesn't connect them with the wrong, dangerous, people.
Software tool Radar is the latest effort to allow parents to retain Big Brother-like control of phones used by their children. It allows parents to monitor all activities on their child's phone; this includes email, text messaging, instant messaging and voice calls.
Parents can create an authorised contact list. Any communication received from someone not on the list is reported immediately to parents via e-mail or text messaging.
"Many bullies and child predators groom children online and then use a mobile phone to contact that child to arrange a face-to-face meeting. Radar can stop them in their tracks," says Bob Lotter, chief executive of Radar developer eAgency.
Details of all incoming and outgoing activities are monitored and a log is kept for viewing at a later date. Parents have the ability to read their child's email, mark certain messages as suspicious or approved and track suspicious patterns in message exchange.
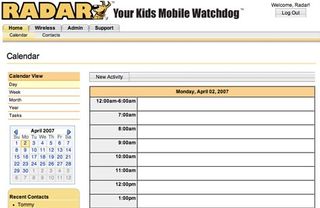
All this is controlled via a web interface. Here, parents not only have access to all the software's features but to resources on locating registered sex offenders, educational safety resources and even a text message dictionary which will help parents translate and understand online lingo.
Get the ITPro. daily newsletter
Receive our latest news, industry updates, featured resources and more. Sign up today to receive our FREE report on AI cyber crime & security - newly updated for 2024.




