MacBook hacker reveals potential iPhone security hole
The researcher responsible for hacking the MacBook in seconds tells of a potential way to break into the iPhone.
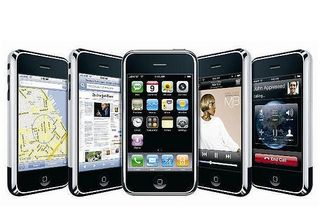
The security researcher who recently hacked into a fully-patched Macbook via Safari in seconds has claimed to have found a security weakness in the Apple iPhone.
Charlie Miller, researcher for Independent Security Evaluators, was one of the first to hack the first generation iPhone. He told of the potential iPhone 3G bug at Europe's Black Hat conference.
Miller claimed that shellcode could be run from the command line of the latest version (2.2.1) of the iPhone operating system. This allows access to the entire file system to run hundreds of different commands.
This was possible on the first version of the iPhone, but it was thought that the latest version of the software was strong enough to prevent this.
Mac security company Intego's blog said that Miller's revelation was currently just a warning, and that an exploit still needed to be written to take advantage of the flaw.
It said: "Mac OS X can run shellcode in fact, many trojan horses exploit this ability but this is an inherent part of the operating system.
"The real issue is exploits that may be able to launch this code on an iPhone, and we're waiting for those to arise."
Get the ITPro. daily newsletter
Receive our latest news, industry updates, featured resources and more. Sign up today to receive our FREE report on AI cyber crime & security - newly updated for 2024.
The whole talk can be found here.




