IT Pro Verdict
Acronis is one of the best disk imaging products around and this latest version offers a fine selection of server data backup and recovery tools all easily accessible from a central management console. However, we were not impressed with the optional data deduplication feature. Although it returned good storage saving ratios, the extremely poor indexing performance makes it highly unsuited to large businesses whose data changes at a rapid rate.
Acronis has always been one of the top dogs in the disk imaging market and its latest Backup & Recovery 10 software targets businesses of all sizes looking to centralise data protection operations for multiple servers.
In this review we put the Advanced Server version through its paces, with a very keen focus on its optional de-duplication feature.
The software comprises a number of components that can all be installed on a single server. For larger sites, the installation can be distributed to lighten the load. You have a Licence Server, which looks after all your licence keys and provides a central control point which ties in with software deployment.
All the action is handled by a management console from where you create and deploy backup policies and individual jobs, run restore and disaster recovery operations and manage backup devices and hard disk vaults. The latter is looked after by the Storage Node component, which allows vaults to be placed on more than one server.
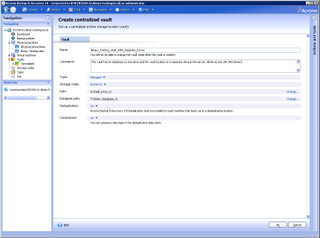
You can create personal vaults, which are backup repositories for the system they are located on but can also be shared amongst multiple systems. For deduplication you need to create centralised managed vaults which are looked after by the Storage Node.
For our management and vault repository system we called up a Fujitsu RX330 S1 rack server loaded with dual 2.3GHz quad-core AMD Opterons, 16GB of memory, 15K SAS drives and Server 2008 64-bit. The Licence Server install takes minutes and then you place your license keys on it for safe storage. We then loaded the main management console and the Storage Node component.
Our next job was to deploy the agents and deduplication components to each server where we pushed them from the management console to Server 2008 and Server 2003 R2 systems. Note that you need a key for each managed server and another for every one you want to apply deduplication to.
Dave is an IT consultant and freelance journalist specialising in hands-on reviews of computer networking products covering all market sectors from small businesses to enterprises. Founder of Binary Testing Ltd – the UK’s premier independent network testing laboratory - Dave has over 45 years of experience in the IT industry.
Dave has produced many thousands of in-depth business networking product reviews from his lab which have been reproduced globally. Writing for ITPro and its sister title, PC Pro, he covers all areas of business IT infrastructure, including servers, storage, network security, data protection, cloud, infrastructure and services.