The KBox scores well with its inventory accuracy. We had a wide selection of systems on the test network ranging from old Pentium 4 workstations right up to systems endowed with AMD Opteron Shanghai' and Intel Series 5500 Xeon processors and Kace picked them all up correctly.
Selecting a computer from the list displays its innermost secrets so you can view all hardware, printers, software applications, installed updates, running processes and much more. For identified software you can view all applications and selecting one will reveal which systems it is installed on.
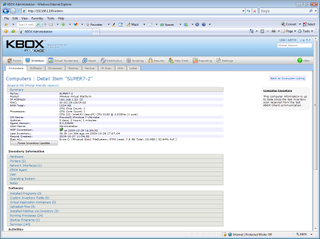
Kace's hardware inventory was on the money and picked up all our Windows 7 systems.
For patch management Kace has teamed up with Lumension and uses its PatchLink service for Windows and Macintosh systems. Unix and Linux system support is in the pipeline and Kace advised us that it's still waiting for Lumension to provide the relevant APIs. Kace has an SLA with Lumension to ensure that all patches are tested and verified by it before being passed on to the appliance.
The optional help desk service enables users to submit trouble tickets via email or the Service Centre web portal. The appliance offers a good range of features as administrators can view all tickets, see their status, assign them to users and change their priorities.
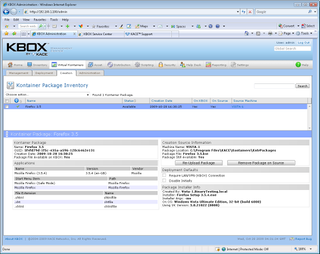
Kontainers are created using a program install file and then exported to selected host systems.
Once a user has raised a support ticket it can be assigned to specific support staff or groups and automatic escalation rules are applied. If a ticket passes its due date of completion it is classed as stalled. The appliance then starts sending out email alerts until its status or priority is updated and it can also change ownership to a new user.
Kace's Kontainers look very interesting as these are designed to present virtual applications to selected systems. A key focus with Kontainers is they enable clients to run applications in a safely isolated environment where all access can be strictly managed.
Dave is an IT consultant and freelance journalist specialising in hands-on reviews of computer networking products covering all market sectors from small businesses to enterprises. Founder of Binary Testing Ltd – the UK’s premier independent network testing laboratory - Dave has over 45 years of experience in the IT industry.
Dave has produced many thousands of in-depth business networking product reviews from his lab which have been reproduced globally. Writing for ITPro and its sister title, PC Pro, he covers all areas of business IT infrastructure, including servers, storage, network security, data protection, cloud, infrastructure and services.


