IT Pro Verdict
LogLogic’s DSM is priced similarly to most competing database security solutions but stands out with its unique vPatch feature as this does away with the need for expensive downtime when applying patches and updates. It’s also easy to deploy and the sensors have no impact on database performance but if you want base lining you will need to factor in the additional cost of an MX or LX log management appliance.
Hardly a week goes by when we don't hear about another database being hacked and vast quantities of personal information being siphoned off. It's easy to criticise but spare a thought for these businesses as they juggle SLAs with the need to monitor, patch and protect their databases.
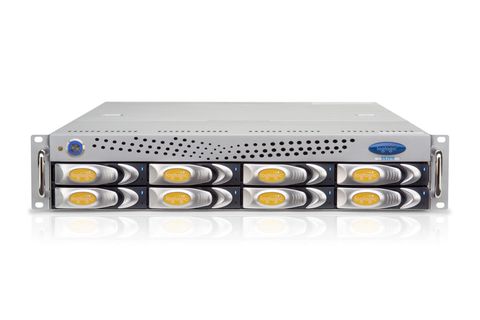
Database monitoring also requires auditing enabled and DBAs are only too well aware of the performance implications this brings. LogLogic's new DSM (database security manager) appliance family is designed to keep the crims at bay but requires no database downtime to deploy and won't have an impact on service performance.
DSM is designed to overcome issues with LogLogic's MX and LX appliances, which, as with all other log management products, require database auditing to be enabled. DSM employs sensors that monitor activity from shared cache memory on the database host. These don't impact on the database but are still able to see all activity including network and local traffic.
The sensors are similar to the IBM Guardium S-Tap software probes, which don't require database auditing to be enabled either but LogLogic's sensors are also capable of enforcing database security policies. There are sensors currently available for Oracle, SQL Server and Sybase ASE 12.3 and these don't require the host system to be rebooted after installation.
One of the most important features of DSM is its unique vPatch. One of the reasons databases are often left vulnerable is businesses simply can't afford the downtime to keep them fully patched and those that do have to schedule deployments which can take weeks to complete.
vPatches overcome these issues as they apply virtual patches to the database. LogLogic takes each patch as it's released by the database vendor and makes them available as vPatches. The DSM's console keeps you posted as new ones are released which can be applied at your leisure without requiring any scheduled maintenance.
Dave is an IT consultant and freelance journalist specialising in hands-on reviews of computer networking products covering all market sectors from small businesses to enterprises. Founder of Binary Testing Ltd – the UK’s premier independent network testing laboratory - Dave has over 45 years of experience in the IT industry.
Dave has produced many thousands of in-depth business networking product reviews from his lab which have been reproduced globally. Writing for ITPro and its sister title, PC Pro, he covers all areas of business IT infrastructure, including servers, storage, network security, data protection, cloud, infrastructure and services.