IT Pro Verdict
Businesses and educational establishments that want quality web content management and monitoring, but don’t want to pay a premium for an appliance, should consider GFI’s WebMonitor. Host hardware requirements are quite reasonable, the software is easy to deploy and it has a good range of top performing security measures and reporting tools.

UTM appliances are a simple one-stop security shop for many businesses but not everyone wants to cough up for the full works, especially if they don't need all those features. GFI's WebMonitor 2011 is a software-based alternative that focuses purely on web content security and is hosted on your own hardware platform.
The latest R3 version supports the ThreatTrack service which uses GFI's SandBox malware analysis tool to check web sites to see if they're harbouring malicious content. These are added to the ThreatTrack data feeds which WebMonitor uses to check sites being accessed so it can block them immediately.
Previous versions had limited IM app controls but, along with Windows Live Messenger, R3 can now block Yahoo! Messenger, Gmail chat and other IM portals including Facebook. Streaming media also comes under WebMonitor's remit and a soft blocking feature allows trusted users to override a warning page and continue browsing.
WebMonitor is available in three versions with the WebFilter Edition enforcing policies for web content filtering, browsing time and media streaming. If you just want anti-virus scanning, phishing protection, IM app controls and ThreatTrack then check out the WebSecurity Edition which uses scanning engines from Norman, BitDefender or Kaspersky.
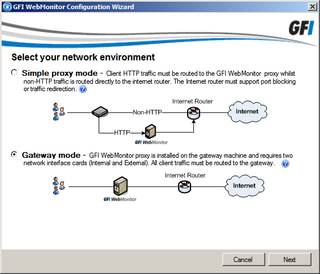
WebMonitor supports two deployments, but the gateway mode is easier as it doesn't need any extra router configuration.
On review covers the UnifiedProtection Edition which combines everything from the other two versions. The price we've shown includes dual scanning engines from Norman and BitDefender. Kaspersky is an extra 12 per seat which does increase costs significantly.
Prior to installation you must decide how you want to deploy WebMonitor. The simple proxy mode only requires one network port on the host, but your router must block all web traffic coming from the LAN. We opted to load it in gateway mode on a Windows Server 2008 R2 system with two network ports as this doesn't require any router changes. Ensure you have all required ports active before loading the software as the installation wizard only offers deployment choices based on what it can see.
Dave is an IT consultant and freelance journalist specialising in hands-on reviews of computer networking products covering all market sectors from small businesses to enterprises. Founder of Binary Testing Ltd – the UK’s premier independent network testing laboratory - Dave has over 45 years of experience in the IT industry.
Dave has produced many thousands of in-depth business networking product reviews from his lab which have been reproduced globally. Writing for ITPro and its sister title, PC Pro, he covers all areas of business IT infrastructure, including servers, storage, network security, data protection, cloud, infrastructure and services.

