The WebMonitor console is a tidy affair that provides a top level dashboard of graphs and tables showing current web activity. Options are provided for viewing general web traffic, blocked sites, the most popular categories and so on. Each panel can be moved around using drag and drop.
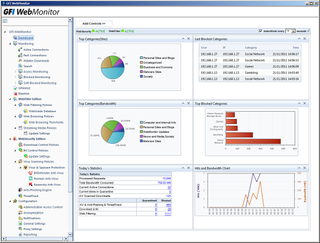
The Dashboard provides plenty of detail on real time web activity and can be customised using drag and drop.
Web access is controlled with policies applied to users, groups and IP addresses. Separate policies are used to manage web content access, browsing periods, anti-virus scanning, streaming media, file downloads and IM apps.
For web filtering you can choose from over seventy WebGrade categories. For each one you can block or allow them, or use the quarantine option which blocks access to a site and makes the user wait for administrative approval.
Selected users and groups may be permitted to browse certain categories or web sites, but time-based policies can be used to restrict how long they can access them for. These limits can be based on daily, weekly or monthly usage or you can apply download limits in KB or MB for these periods instead.
HTTPS scanning comes as standard and WebMonitor provides a wizard that runs through certificate creation. The host system can also cache downloaded files and web content to improve response times.
Virus scanning policies are accessed from the WebSecurity console section. You can choose from a list of file types, pick the engines for scanning and decide whether to delete or quarantine infected files. When downloading files, users can be redirected to a web page showing their progress and only when the file is deemed to be safe will they be allowed to save it to their system.
Dave is an IT consultant and freelance journalist specialising in hands-on reviews of computer networking products covering all market sectors from small businesses to enterprises. Founder of Binary Testing Ltd – the UK’s premier independent network testing laboratory - Dave has over 45 years of experience in the IT industry.
Dave has produced many thousands of in-depth business networking product reviews from his lab which have been reproduced globally. Writing for ITPro and its sister title, PC Pro, he covers all areas of business IT infrastructure, including servers, storage, network security, data protection, cloud, infrastructure and services.

