IT Pro Verdict
The ProSecure UTM9S is a good choice for small businesses that want a low-cost UTM appliance that doesn’t skimp on features. You will need a ReadyNAS appliance for the new logging and quarantining features, but the extra expansion modules make it very versatile and our lab tests show that its anti-spam performance is good.
Netgear's ProSecure UTM appliances have always been affordable gateway security solutions for cash-strapped SMBs. Its latest UTM9S is its first to have a pair of modular expansion slots and integration with the company's ReadyNAS storage appliances.

This desktop box is positioned between the UTM5 and UTM10 appliances and has claimed throughputs of 130Mbit/s for its SPI firewall and 21Mbit/s with anti-virus (AV) scanning enabled. Netgear doesn't apply per-user licenses, but we reckon the UTM9S is good for at least fifteen users.
The UTM9S has the same software features as all the other UTM appliances which include an SPI firewall, IPS and support for IPsec and SSL VPN tunnels. Netgear's security partners need no introduction as you have Mailshell handling anti-spam, Sophos dealing with viruses and malware and Commtouch stepping up for URL category filtering.
The appliance has four Gigabit Ethernet ports for LAN duties and two more for WAN connections which can be placed in load balanced or failover teams. Traffic metering can also be enabled on any of the WAN ports including any expansion cards. This enforces monthly upstream and downstream limits in MB and either blocks all web traffic or allows only email when these thresholds have been breached.
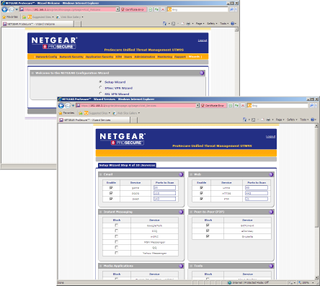
The web browser's wizard had us up and running in minutes.
The UTM9S functions as a transparent gateway so installation is a cinch. For testing we dropped it between the lab network and our Internet link and the web browser's wizard had us up and running in minutes. The appliance is preconfigured with two firewall rules to look after inbound and outbound traffic. You can add custom firewall rules if you wish and apply bandwidth restriction and quality of service (QoS) profiles to selected services.
ReadyNAS integration requires an add-in to be installed on the storage appliance after which it can be used as a quarantine area and remote log store. Previously, if you powered off a UTM appliance all its logs and Flash-based graphs and statistics tables were lost.
Dave is an IT consultant and freelance journalist specialising in hands-on reviews of computer networking products covering all market sectors from small businesses to enterprises. Founder of Binary Testing Ltd – the UK’s premier independent network testing laboratory - Dave has over 45 years of experience in the IT industry.
Dave has produced many thousands of in-depth business networking product reviews from his lab which have been reproduced globally. Writing for ITPro and its sister title, PC Pro, he covers all areas of business IT infrastructure, including servers, storage, network security, data protection, cloud, infrastructure and services.

