Next we ran Norton and Webroot head to head, checking the URLs on a list of known infected domains. Of these thirty were verifiably still live and hosting malware. Webroot spotted 13 of these; Norton spotted fourteen.
Interestingly, the two programs detected only five in common, so for web protection you'd be better off running the two together. Both programs let us visit three that were clearly untrustworthy and which even Google Chrome's own database flagged up as risky. Google Chrome did better than either program, flagging all thirty sites as hosting malware.

There were instances where Chrome warned us that something's wrong but SecureAnywhere let us access the website anyway
As a final test, we downloaded a selection of zip files containing 60 viruses. SecureAnywhere had trouble with a few older Linux viruses, which it didn't recognise. On the other hand, it was able to find the spyware W32.Trojan.Gen, which F-Secure missed. Aside from that, its performance was consistent with that of F-Secure and Symantec's software.
Manageability and reporting
Vendors are increasingly offering businesses increased levels of flexibility and control. Webroot's control panel is easy to use and gives customers plenty of options to create flexible policies suitable to different kinds of users.
A big selling point of SecureAnywhere is its manageability. As it's cloud-based you can connect to the console from anywhere. Handier still is the policy-based administration, which is a great feature. As you would in Active Directory, you can organise users (identifiable by their computers' NetBIOS names) into groups then create policies and apply them to those groups.
IT admins may want to prevent most users from opening the SecureAnywhere application, disabling it or even seeing it running in the taskbar. You can do this easily with SecureAnywhere, whilst still allowing more experienced or trusted users higher levels of access.
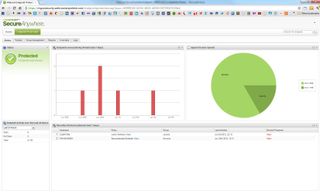
The web console is easy to use and gives you fairly precise control over user settings along with plenty of scope for customisation
SecureAnywhere also provides eight pre-defined reports. These include information such as which versions of the Webroot agent are installed and which clients have outstanding threats. The reporting feature we liked most was "Endpoints with undetermined software". This shows you all the clients with unidentified software installed. It's a eye-opener and will be very useful when you're trying to track down problems.
Overall
The Webroot client is amazingly light and easy going on system resources, which makes it great for businesses which may have dated machines.
Although SecureAnywhere has a few blind spots, most noticeably letting us surf some obviously suspect web sites, it is able to detect major threats with the same rigor as its main desktop rivals.
If you don't want to trust SecureAnywhere on its own, you could use it as an extra layer of security. Unlike most other anti-virus software, SecureAnywhere can co-exist with its rivals. We installed it on the same systems as both of our control programs (Symantec and F-Secure) without any problems at all.
Verdict
Webroot SecureAnywhere did as well as its competitors in most of our tests, and was up to 10 times faster when it came to scanning. We like the the use of the cloud as virus signatures are kept up-to-date and the precision with which it lets you manage users makes it attractive. The eight reporting tools round off a set comprehensive features, which will be of use to IT admins.
Available for Windows XP/Vista/7, Windows Server 2003/2008/2010, 128MB RAM, 10MB hard disk space required
