Load balancing schedules
The web interface is the same as previous editions and could do with some graphical refreshment as it's looking dated. Even so, it is simple to use and provides easy access to each feature.
For testing, we fired up a Dell PowerEdge R515 rack server running Windows Server 2008 R2 and the Hyper-V role. We created multiple Server 2008 R2 VMs all running IIS web services.
To create virtual servers, you provide an IP address, port number and protocol and then you can add physical servers to your farm. Kemp now offers eight load balancing, or scheduling schemes with it defaulting to round robin mode which distributes client requests to each server in strict rotation.
Weighted round robin allows priorities to be assigned to each server in the farm to ensure better specified servers get the lion's share of the work. Servers with the least number of connections can be prioritised and you can apply weighting to control which are used the most.
Weighted response time dynamically adjusts weights for each server based on their response times and the new source IP hash schedule ensures the same real server is always used for a specific client. Load balancing can be adapted to server performance using a local agent on each physical server. This presents a web page with a numerical value between 1 and 100 to a LoadMaster query that defines how busy the server is.
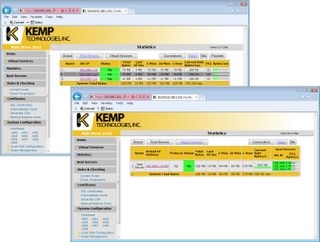
Statistics screens keep you posted on throughput and load balancing performance for the virtual and real servers
Dave is an IT consultant and freelance journalist specialising in hands-on reviews of computer networking products covering all market sectors from small businesses to enterprises. Founder of Binary Testing Ltd – the UK’s premier independent network testing laboratory - Dave has over 45 years of experience in the IT industry.
Dave has produced many thousands of in-depth business networking product reviews from his lab which have been reproduced globally. Writing for ITPro and its sister title, PC Pro, he covers all areas of business IT infrastructure, including servers, storage, network security, data protection, cloud, infrastructure and services.

