IT Pro Verdict
Combine the well-designed web portal, user based policies and top-notch mobile support and you have a quality cloud endpoint security solution. Sophos Cloud isn’t the cheapest but we think it’s well worth the extra outlay.
Pros
- +
Easily managed; User-based security policies; Excellent mobile device support; Classy cloud portal
Cons
- -
Lengthy client install
Endpoint security has traditionally been a tough nut to crack across businesses of all sizes as many solutions have a reputation for being difficult to deploy, a nightmare to manage and inconveniently expensive. These problems are exacerbated by the exponential growth of corporate mobile devices making it nigh on impossible to protect them all.
Worry not as the cloud is coming to the rescue of businesses frightened off by these concerns and Sophos Cloud is one of best solutions we've yet seen. Along with cloud managed anti-malware, web filtering and removable device controls, it offers tough security measures for iOS and Android devices.
It's also a top choice if you want your security policies to apply to users as well as devices. In our books, this makes Sophos Cloud highly versatile as we used it to create security policies that followed users regardless of which device they logged in from.
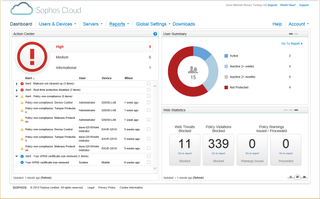
The Sophos Cloud portal provides plenty of information about endpoint security events and alerts.
Slick cloud portal
After signing up we were provided with our own dedicated cloud portal which gave us access to every feature. Its dashboard comprises three big panels with clear overviews of all alerts, activities and web stats.
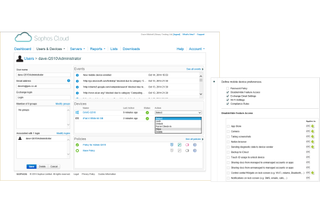
The next tab provides views of your users, groups and devices plus options to enable iOS support. It's here that you also create security policies and monitor Active Directory users and groups.
The new server protection feature applies custom policies to these systems. They are more basic than standard policies but provide a range of tough measures including real-time and scheduled malware scanning, automatic blocking of known malicious web sites and Sophos' HIPS (host intrusion prevention system) which watches out for suspicious program behaviour.
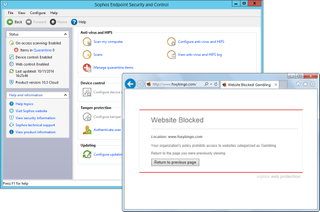
Web filtering works well and, if permitted, users can play with the Sophos client software
Lengthy deployment
For testing we used the main lab network headed up by a Windows Server 2012 R2 Active Directory domain controller running the Hyper-V role and hosting an Exchange 2013 VM. For desktops we used a bunch of Windows 7, 8 and 8.1 hosts while for mobile testing we used an iPad 4.
Software deployment to our Windows systems was lengthy as the installer utility downloads the entire 156MB agent package for each one. A single install took up to 15 minutes whereas simultaneous installs on four devices took a total of 25 minutes.
It speeded up after this, though, as the agent was preconfigured for our account and each system appeared in the portal in seconds. Sophos also adds details of the current user logged in when the agent was installed and we used the new AD Sync tool to import users from our AD server.
We had problems with AD Sync's secure LDAP mode as it refused to access our server. Online help is minimal but we fixed it by selecting non-secure LDAP mode and changing the port number.
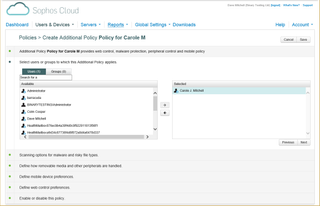
After importing our AD users we could assign custom security policies to each one
Policies and performance
Despite the focus on user-based protection, static devices such as desktops aren't left out in cold as a base security policy is applied to everything. The real-time malware scanner is enabled by default, access to removable media can be restricted or monitored and anti-tamper controls are active.
For web filtering, we could tweak the base policy or create new ones and choose from a wide range of settings. These include blocking dodgy file downloads, using one of four predefined URL filtering policies or setting our own web usage restrictions.
Alert responses are fast as after introducing real malware to our clients, the Action Center pane changed to red alert status in only 25 seconds. This was the same amount of time it took to push out a global USB storage device block policy.
A remote quick scan request to a Windows Server 2012 R2 system was fired up in less than 20 seconds and completed in 5 minutes while a locally run full scan of its 72GB system drive took 47 minutes. Sophos is a safe pair of hands as well with it scoring 96% for AV-Test's zero-day detection and returning a clean sheet in the widespread malware test.
Sophos offers extensive mobile device security features and includes options for iOS remote locks and wipes
BYOD beware
For mobile devices controls, iOS gets the lion's share. Along with passcode and complexity enforcement, we could control access to features such as the App Store, camera, screenshots and iCloud backup.
We also used policies to control which wireless networks mobile users could connect to and request alerts if their OS versions weren't up to date. Web filtering rules are on the cards and policies can be used to set company Exchange Server credentials.
Deployment to our iPad 4 required an Apple Push Certificate created and a download link for iOS emailed to the mobile user via the cloud portal. Once the Sophos Mobile Control app connected, it enforced our passcode policy, controlled access to apps by removing the icons for blocked ones and allowed us to issue remote lock and wipe commands from the portal.
Conclusion
Sophos Cloud is more expensive than products such as Trend Micro's Worry-Free cloud service but it beats everyone soundly for features. Its lightning quick portal, user based policies and top-notch mobile device support earns it a well-deserved Editor's Choice award.
Verdict
Combine the well-designed web portal, user based policies and top-notch mobile support and you have a quality cloud endpoint security solution. Sophos Cloud isn’t the cheapest but we think it’s well worth the extra outlay.
Agent: Windows XP Pro and Server 2003 upwards, Mac OS X 10.7 upwards. Mobile: iOS 7, Google Android 4.0 upwards
Dave is an IT consultant and freelance journalist specialising in hands-on reviews of computer networking products covering all market sectors from small businesses to enterprises. Founder of Binary Testing Ltd – the UK’s premier independent network testing laboratory - Dave has over 45 years of experience in the IT industry.
Dave has produced many thousands of in-depth business networking product reviews from his lab which have been reproduced globally. Writing for ITPro and its sister title, PC Pro, he covers all areas of business IT infrastructure, including servers, storage, network security, data protection, cloud, infrastructure and services.



