How to catch hackers in the act
The best tools for keeping track of when someone accesses your internet, computer, phone and more

No matter how well protected your computer is, all systems can be compromised. In many cases, this happens under our very nose and it's almost impossible to catch a hacker red-handed as they try and access your files or take control of programs.
Fortunately, there are early-warning tools available that can immediately alert you to any system breach, whether that's someone trying to take over your webcam or trying to make changes to your files. The great thing is that the majority of these tools are free, although they don't always come with the most user-friendly of setups.
We've put together a list of potential hacking scenarios and the tools you should consider trying out in order to combat them.
When new devices connect to your network
Worried that someone's leeching off your internet? An easy way to find out for sure is to use Nirsoft's Wireless Network Watcher, which lists connected devices on your network. Wringing every last function out of this feature-rich program would take days, but even at its most basic, it reveals plenty about network activity.

Find out when devices are connecting to your network
Run Wireless Network Watcher, then click the column marked Last Detected On until it displays a down-arrow. That way, the newest device to connect always shows at the top. This helps you recognise it at a glance.
To set up alerts for potentially rogue devices, enter Options and turn on Beep On New Device and Beep On Disconnected Device. Remember to turn up your volume. Now, head into Device Options. Here, you can set your own connection and disconnection alerts if you don't like the defaults maybe an air raid warning siren? Finally, create a log by selecting View and choosing HTML Report All Items.
Get the ITPro. daily newsletter
Receive our latest news, industry updates, featured resources and more. Sign up today to receive our FREE report on AI cyber crime & security - newly updated for 2024.
When changes are made to your system
If you're concerned about ransomware, or just don't want anyone toying with your rig, download WinPatrol your digital guard dog. Features include controlling startup programs and delaying chosen programs from running at boot-up, which speeds up your computer.
After recoiling at how badly designed the user interface is it's visually busy, crammed with 15 tabs, and absolutely no directions for use you can start monitoring changes to your computer's files and folders.

WinPatrol.png WinPatrol helps protect you from malware and worse
WinPatrol can be used as a purely passive program. Leave it chugging away in the background and whenever a new program runs, or attempts to install, it'll give you a heads-up in the form of a visual and audio alert. You're then able to accept or reject any changes. Don't recognise the program? Reckon it might be malware or worse? Block it from running or ruining your PC.
It's worth noting that this only halts programs you'll need to track them down in WinPatrol to begin the process of removing the threat.
When someone accesses your shared files
Sharing is caring. It's also usually secure when doing so over your own network (just be sure to change your default WiFi password). Don't be lulled into a false sense of security, though. Download Net Share Monitor (bit.ly/net463) to keep a close eye on all shared folders.
It's a pleasantly minimalist tool. Just three tabs sit in the window: Active Sessions logs remote users, Accessed Files displays which folders and files remote users are currently connected to, while Shared Files lists the network's shared folders.

Track every change when sharing over your network
Microsoft offers a decent guide to sharing folders, available here. Once complete, let the tool go to work. Net Share Monitor automatically finds and scans shared folders, with no additional setup required. The instant that changes are detected, it'll beep and flash, while logging details in a separate file.
For a cloud storage alternative, OneDrive sends emails and push notifications to your phone whenever users open shared files and make alterations.
When changes are made to your folders
FolderMonitor is the local equivalent of Net Share Monitor. After you download it, the program's likely to be lurking in your system tray, so double-click the icon and force it open.
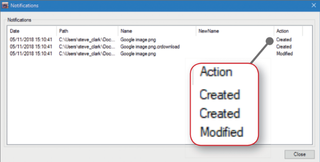
Place folders under surveillance with FolderMonitor
Right-click anywhere in the window, then select 'Add folder'. Find the folder you want to observe, and click Ok to add it to the watch-list. Alternatively, 'Add path' lets you cast a wider net (for instance, placing every folder in This PC under surveillance).
When a folder is added to FolderMonitor, right-click it to open FolderMonitor Options. Choose the events you want to check for Created, Changed, Renamed, and Deleted. Now, when an unscrupulous someone takes remote control, it triggers an unmissable alarm, warning you of changes to the offending folder.
When someone logs into your PC
Need to keep your computer under lock and key while you're away? Use Microsoft's Task Scheduler to send an email every time someone logs onto your machine.
Ironically, in order to run this, you'll need to turn on 'Less secure apps' for your Google account as such, we suggest creating a dummy Gmail address specifically for these notifications.
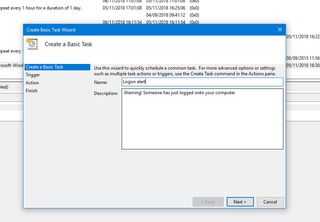
Set up an automatic alert when someone logs onto your computer
First, download and extract SendEmail. Then, forget about it. We're going to perform a mini-workshop instead. Open Windows Task Scheduler. On the Actions panel, click Create Basic Task, and give it a name and description. In the Trigger tab, tick 'When a specific event is logged'. Hit Next and under Log, use the drop-down to select Security; under Source, choose 'Microsoft Windows security auditing'. In the ID box, type 4624. Click Next.
On the Action page, click 'Start a program' and choose SendEmail. In the 'Add arguments' box, type the following, replacing everything in brackets with your own data: -f [fromemail]@gmail.com -t [toemail]@gmail.com -u [Subject line, e.g. Did you log on?] -m [Message, e.g. Someone's logged onto your computer] -s smtp.gmail.com:587 -xu [fromemail]@gmail.com -xp [fromemail password] -o tls=yes
Once that's done, test the automated alert by locking and unlocking your computer. You should receive an email warning you of the login.
When an app tries to spy on you
Have you ever downloaded a seemingly innocuous app, and wondered 'Why would it need to access my microphone and camera?' Well, it could be that the devs are spying on you. Even legitimate apps like Facebook have come under fire for supposedly listening in (for targeted advertising reasons, of course).
To take control, check every app's permissions in Settings then revoke access to sensitive tools such as the microphone, camera, Bluetooth, Wi-Fi and location (or ditch the app entirely if you don't trust it).

D-Vasive Anti Spy monitors apps that may be watching you
For extra protection, you can download D-Vasive, created by self-proclaimed 'cybersecurity legend' John McAfee. Note that it costs 4.49. But while there are free alternatives, we've yet to find one that fully replicates D-Vasive's protective security measures; D-Vasive sends alerts every time an app activates smartphone tools that may record, track, or otherwise spy on you. Whenever a warning flashes, you can instantly shut it down.
Get alerts when your accounts are breached
Is it time to change your username and password again? It seems like every week brings a fresh hack or cyber-attack to worry about.
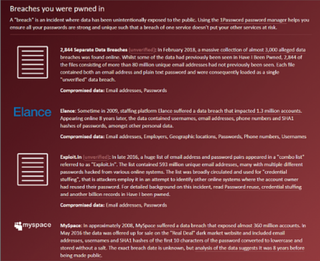
Have you been pwned?
Haveibeenpwned.com cross-references your email address against accounts that have been hacked, stolen and sold on the dark web. As well as searching its database, you can protect yourself against future breaches by setting up email notifications via bit.ly/pwnme463, so you're informed as soon as the attack happens and can change your login pronto.
For extra security, install the HackNotice extension for Chrome. This handy browser tool tells you when you're visiting a site that's been hacked. You can even set up a watchlist for sites you regularly visit, or those that store personal data.




