Witcher 3 dev forums hacked, 1.8 million accounts stolen
Usernames, passwords and email addresses stolen from the CD Projekt RED forum

Polish game development studio CD Projekt RED has had more than 1.8 million user credentials stolen from its online forum, according to data breach notification website 'Have I Been Pwned?'.
The studio, which is famous for developing the highly successful Witcher franchise, was breached in March 2016 when hackers targeted its online forum, leading to a leak of usernames, passwords and email addresses.
Those signed up to notifications through Have I Been Pwned? were alerted to the breach by email this morning, with users recommended to change their passwords "immediately".
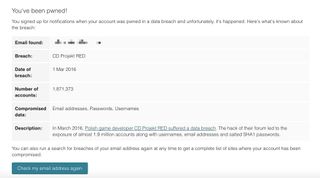
"Whilst the breach occurred in March 2016, sometimes there can be a lengthy lead time of months or even years before the data is disclosed publicly," the message stated, in an email seen by IT Pro. "Have I Been Pwned? will always attempt to alert you ASAP, it's just a question of how readily available the data is."
According to the site's creator, security researcher Troy Hunt, a total of 8,110 individual subscribers received breach alerts, considered a high rate for notifications.
The forum, which is hosted on CD Projekt RED's main website, acts as a news and discussions hub, providing users with gameplay advice and technical support.
The sheer number of affected accounts represents one of the most significant data breaches to have affected a gaming community. Hackers also targeted development studio Epic Games in August 2016, when 800,000 account details were stolen from its gaming forums, although that number is now dwarfed by the latest breach.
Get the ITPro. daily newsletter
Receive our latest news, industry updates, featured resources and more. Sign up today to receive our FREE report on AI cyber crime & security - newly updated for 2024.
E-sports organiser ESEA, which coordinates events for the massively popular Counter Strike, also suffered from a botched ransomware attack in December, which ultimately led to 1.5 million accounts being leaked online as a result.
IT Pro has approached CD Projekt RED for comment but did not receive a reply in time for publication. We will update this story when we hear more.
Main image credit: Thomas McMullan
Dale Walker is the Managing Editor of ITPro, and its sibling sites CloudPro and ChannelPro. Dale has a keen interest in IT regulations, data protection, and cyber security. He spent a number of years reporting for ITPro from numerous domestic and international events, including IBM, Red Hat, Google, and has been a regular reporter for Microsoft's various yearly showcases, including Ignite.





