Seven ways to test your online security
The best online tests for identifying security blind spots

You may have all the latest security tools installed, you may follow best practice and avoid suspect emails, and you may never reuse the same password twice, yet there can always be a chink in your cyber security armour.
Sometimes this can be something simple, such as failing to update software, or more intricate, like an open port on your network. Fortunately, there are free tools available online that can deep dive into your defences to see just how robust they are.
The problem is knowing exactly where to go and who to trust - so we put together a list of the some of the best tools and scanners out there to make things easier.
Check if your accounts have been breached
If you suspect you may have fallen victim to a hack, visit Have I Been Pwned? which catalogues all the email addresses and other data taken in high-profile breaches.
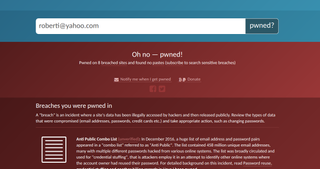
Search for your address, and if it's found in the data dumps, a red warning will appear, revealing what was taken in the hack and recommending you change your password(s) immediately. You can also sign up for notifications of future breaches. At the time of writing, Have I Been Pwned? featured more than 4.7 million 'pwned' accounts and 232 'pwned' websites, including MySpace, Adobe and LinkedIn.
Test the strength of your passwords
There are lots of online tools that test the strength of your passwords, but make sure you use one that encrypts what you enter or you could actually be risking your security.

Our favourite it the Dashlane-sponsored How Secure Is My Password, which tells you how long your password would take a hacker to crack. If the answer is only seconds or minutes, you should change the password as soon as possible.
Get the ITPro. daily newsletter
Receive our latest news, industry updates, featured resources and more. Sign up today to receive our FREE report on AI cyber crime & security - newly updated for 2024.
Ensure your security software is working
Don't let malware infection be the first sign of a security hole The Anti-Malware Testing Standards Organization (AMTSO) offers a Security Features Check that exposes potential weaknesses in your system's defences.
The check consists of six tests, four of which involve downloading files that your PC should identify as malware and block automatically. These files aren't actually malicious but are designed to be detected as such, so if your anti-malware program lets one through, then you need to tighten your settings.
Test your firewall for weaknesses
Firewalls generally run quietly in the background, so it's important to know that they're working properly. To test yours, try to bypass it using the free online port scanner GRC ShieldsUP.

Ports should be closed by default aside from port 80 (or 443), which is needed for web traffic. You can choose to test either Common Ports (only the most vulnerable ports) or All Service Ports (a thorough scan of 1,056 ports). Green or blue results mean that those ports are secure, while red ones show open ports that need to be closed.
Ensure your plugins are up-to-date
Security holes in Java, Adobe Reader and Flash put your personal data at risk, so ensure your plugins are up to date using Qualys BrowserCheck.
This scans your browser and its plug-ins to detect outdated versions and other security problems. Click the Fix It button next to scan results marked as 'insecure version' or 'update available' to install the required updates. The test works with all major browsers.
Check your Facebook security
Facebook now offers a Security Checkup tool that lets you review and lock down your account. Go here and Facebook will tell you whether you're still logged into the social network in a browser or app you haven't used for over a month. You can also set up login alerts to be notified via email when if your account is accessed from an unrecognised device or browser.
Test your own security knowledge
Avoid being the weak link in your PC's protection by keeping your security knowledge up to scratch. There are lots of online quizzes that test your ability to spot online threats, including BT's Security Savvy test and the OpenDNS Phishing Quiz.
Image: Shutterstock




