GoldenEye ransomware disguised as job application
Opening the Excel attachment will encrypt the files on your computer
Check Point has uncovered a ransomware attack that is targeting German HR managers by posing as a legitimate job application.
The email is sent with a harmless PDF covering letter and an Excel spreadsheet that contains the ransomware. When the victim opens the Excel spreadsheet, they are invited to enable content so the macros can run. Upon giving the go-ahead, the malicious macro will launch a program that encrypts all the files on the user's computer, presents the message "YOUR_FILES_ARE_ENCRYPTED.TXT".
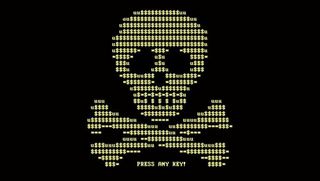
While the files are being encrypted, the user is faced with a fake "chkdsk" screen, urging them not to turn off their PC. When all the files are encrypted, they will see a skull and crossbones and be told their files have been encrypted using GoldenEye, with instructions of how to pay the ransom and unlock their files. The rates to unlock files start at 1.3 Bitcoins (800) per infection.
"Despite trying to brand itself as a new malware, GoldenEye, the latest Petya variant, is very similar to older versions and differs mostly in its "golden" motif," Check Point explained. "The most prominent change, however, is how the campaign spreads the ransomware.
"The current campaign used to distribute GoldenEye has a job application theme. It is therefore aimed at companies' Human Resources departments, due to the fact they usually cannot avoid opening emails and attachments from strangers, a common malware infection method."
The researchers said the campaign has only been running for a few days and it seems as though the infected attachment has been given a number of names, making it even more confusing for recipients. However, they follow the same format, with the supposed candidate's name as the first part of the file name and "Bewerbung", meaning "application" in German, as the second part.
Main image credit: Check Point
Get the ITPro. daily newsletter
Receive our latest news, industry updates, featured resources and more. Sign up today to receive our FREE report on AI cyber crime & security - newly updated for 2024.

Clare is the founder of Blue Cactus Digital, a digital marketing company that helps ethical and sustainability-focused businesses grow their customer base.
Prior to becoming a marketer, Clare was a journalist, working at a range of mobile device-focused outlets including Know Your Mobile before moving into freelance life.
As a freelance writer, she drew on her expertise in mobility to write features and guides for ITPro, as well as regularly writing news stories on a wide range of topics.




