IT Pro Verdict
The refreshed design brings with it a number of core features. But with Google set to unveil Android Kit Kat 4.4 in October, Apple may quickly find itself behind its chief rival once again.
Pros
- +
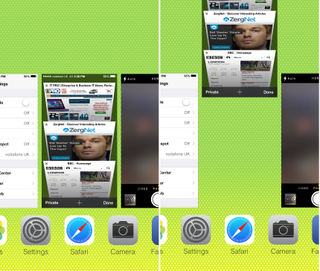
Colourful redesign; Improved navigation; Best gesture control yet
Cons
- -
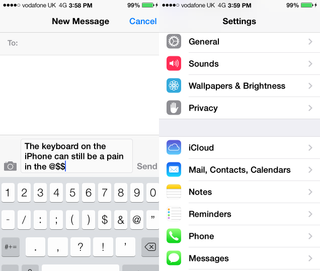
Still no choice of keyboard; Some apps need to be fixed; Older devices will struggle
iOS 7 has landed on iPhones and iPads across the globe, and demand for the software update has been unprecedented.
Here we go through the pros and cons of the mobile operating system to see what Apple has improved, upcoming features and areas of iOS that still need work. Don't forget to check out our top tips for optimising iOS 7 and also the lowdown on the core business features Apple has built. Features we love



Upcoming features
- iCloud keychain - Apple is making a strong play to try and eliminate the need for traditional passwords. The firm has included a fingerprint scanner on the iPhone 5s and plans to release its iCloud Keychain software to supplement this.The iCloud keychain will work in conjunction with Safari to remember account names, passwords and credit card details. The web browser will enter credentials automatically when required and Apple claims these details will be protected by 256-bit AES encryption. We're sure hackers will put this system to the test just to see how secure it really is when it is launched.
- OS in the Car - This feature will allow users to connect their iPhones to the built-in display within cars and control features using the on-board controls or Siri Eyes Free. Features include the ability to make phone calls, play music, send/ receive messages and get directions. So far 19 manufacturers, including BMW, Mercedes, Ford and Toyota, have shown interest in deploying this across their fleet, but there is no time frame for release.
Areas in need of improvement
Verdict
The refreshed design brings with it a number of core features. But with Google set to unveil Android Kit Kat 4.4 in October, Apple may quickly find itself behind its chief rival once again.
Compatible with iPhone 4 + later, iPad 2 + later, iPod Touch 5th Gen and iPad mini

