AdaptiveMobile uncovers RAT mobile malware
The malware is sent via SMS that redirects to an APK file
AdaptiveMobile has discovered mobile malware that will allow a hacker to remotely control or monitor the phone, listening in to conversations, tracking any web activity and hijacking the camera when it wishes to.
The remote access control (RAT) malware is sent to a smartphone via SMS. If a user clicks on the link in the message, they will be redirected to an APK file. If this is opened, it will install the malware on the device, allowing the criminal to take over.
"While unsophisticated, this malware is interesting as it is delivered using SMS and is purporting to be a MMS message," AdaptiveMobile said in its report. "We've seen this specific behaviour before in Russia in 2013. And as we've reported on before, the normal propagation method for malware using SMS is via worms."
The APK is packaged using DroidJack, which is unique to Android devices and is easy to package for even the most junior of hackers. In fact, a hacker could package the malware using a tutorial readily available on the DroidJack website.
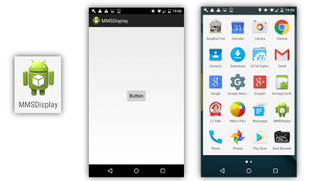
Another indicator that the person or group behind the malware is not a professional is that they did not attempt to hide the malware. Rather than injecting the it into another application to launch an attack without the user knowing, the RAT malware takes the name of MMSDisplay.
"This is not the first time the attacker has attempted to exploit mobile users," AdaptiveMobile said. "We observed the same number sending PayPal phishing spam to North American subscribers, with the phishing website tracked to be hosted at the same location as the malware."
The company reminded people not to click on the link in an SMS from an unknown sender to prevent the malware infecting their device.
Get the ITPro. daily newsletter
Receive our latest news, industry updates, featured resources and more. Sign up today to receive our FREE report on AI cyber crime & security - newly updated for 2024.
"While we often demonstrate the increasing sophistication and complexity of attacks on mobile networks, it's important to remember that a simple attack can also be a success for the attacker," the company said.
"As security controls become tighter and mobile operators work to identify and block attacks on mobile networks, bad actors are using a variety of methods and moving to different bearers."

Clare is the founder of Blue Cactus Digital, a digital marketing company that helps ethical and sustainability-focused businesses grow their customer base.
Prior to becoming a marketer, Clare was a journalist, working at a range of mobile device-focused outlets including Know Your Mobile before moving into freelance life.
As a freelance writer, she drew on her expertise in mobility to write features and guides for ITPro, as well as regularly writing news stories on a wide range of topics.




