IT Pro Verdict
Kaspersky’s Endpoint Security provides top-notch malware detection and is easier to deploy than competing products. The Security Center console provides good centralised management facilities and offers quality reporting and alerting features.
Pros
- +
Easy deployment; Well designed console; Top anti-malware performance; Detailed reporting
Cons
- -
Not the best value
Deploying network security software can be a daunting prospect for many SMBs but Kaspersky aims to make it a easier and less complicated. Endpoint Security for Business (ESB) offers a range of options including anti-malware for servers and workstations, patch management and mobile device security but all can be deployed and managed from a single console
ESB is available in four versions. You can start with basic protection and expand it with extra modules as demand dictates. We reviewed the base Core edition which comprises the Security Center console and anti-malware for workstations.
The Select edition adds file server and mobile device protection plus application controls. The Advanced edition brings in encryption and systems management while Total Security bolsters this with mail server, gateway and collaboration security. Each package can be expanded with extra modules as the need arises.
Security Center takes a few minutes to install and it then goes off and loads all relevant updates and signature databases from the Kaspersky support site. The main console hasn't seen any major design changes for a few years but, unlike AVG's Business Edition 2013, it doesn't need any.
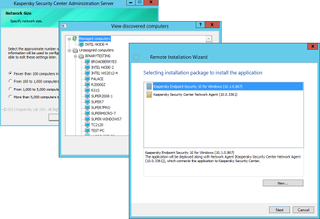
The security suite can be easily deployed using a choice selection of methods including network discovery
Deployment
There are plenty of workstation deployment options and it's worth checking them all out to ensure you use the best method. The console's search facilities show anything from subnet or workgroup contents to lists of Active Directory (AD) computers.
The Network Agent and Endpoint Security components can be deployed manually by selecting multiple systems from one of the searches and pushing both components to them with one job. Alternatively, you can pick a single system and fire the software straight at it using its drop-down menu.
Automatic installation is the quickest way as all unassigned systems can be added to a console group with this feature enabled and it'll go ahead and do it all for you. There's more as a wizard can create a group structure based on a selected workgroup, domain or AD, populate it and run the entire deployment.
For testing we used virtual Windows XP, 7 and 8 clients hosted on VMware ESX and Hyper-V servers. All systems were AD domain members and all were listed correctly by the console search facility.

The Security Center administrative console is well designed with plenty of information about workstation status
Security policies
Work deployment takes at least 15 minutes per system which is slower than AVG's Business Edition 2013. However, we found Kaspersky to be less resource hungry with CPU usage rarely going over 50 per cent on any virtual client during this phase.
Group policies control how the Network Agent and Endpoint Security behave and are applied when a client joins a group. You can create sub-groups which inherit settings from the top level or have their own policies.
Lists of group members can be viewed from the console and their multi-coloured icons provide at-a-glance status indicators. You can drill down into each client's properties, view status reports and run tasks such as full system scans or updates on them.
With group polices in action, users can't fiddle with the Endpoint Security client settings but they can load its console, see what's occurring and run custom malware scans. Along with scanners for files, email, web and IM traffic, you get a client firewall, a network attack blocker and a system watcher that keeps an eye out for suspicious application behaviour.

Tasks such as virus scans can be fired off swiftly to all group members
Performance and reporting
Policies also keep users out of the decision process when malware is detected. When we introduced a selection of malware to our test clients, Endpoint Security blocked them all, disinfected or deleted the dodgy files, posted warnings in the Security Center console and alerted us via email.
Kaspersky never disappoints for malware detection performance. In the latest Dennis Technology Labs Enterprise Anti-Virus Report, Kaspersky grabbed the top slot ahead of Symantec, Microsoft, Trend Micro and McAfee with a near perfect score.
Reporting is another area where Kaspersky does well. Whereas AVG's reporting tools look prehistoric, the Security Center console offers copious event lists and reports for nearly every occasion.
These include detailed and exportable HTML reports on detected malware, the most infected systems, users, errors, client protection status and much more. Endpoint Security also gathers registry information on each client allowing the console to furnish you with hardware and software inventory reports.
Users can be permitted to access their local Endpoint Security dashboard and view their protection status. This provides a report of all detected malware and a network monitor lets them see how much inbound and outbound traffic each of their applications is generating.

The console keeps you posted on all malware activity and provides extensive reporting facilities
Conclusion
Kaspersky's Endpoint for Business Core is more expensive than competing products but we think it's worth the extra cash. It's easy to deploy, can be upgraded with further security features as required and the workstation anti-malware components perform well.
Verdict
Kaspersky’s Endpoint Security provides top-notch malware detection and is easier to deploy than competing products. The Security Center console provides good centralised management facilities and offers quality reporting and alerting features.
Windows XP SP2 upwards; includes Endpoint Security for Windows, Linux and Mac
Dave is an IT consultant and freelance journalist specialising in hands-on reviews of computer networking products covering all market sectors from small businesses to enterprises. Founder of Binary Testing Ltd – the UK’s premier independent network testing laboratory - Dave has over 45 years of experience in the IT industry.
Dave has produced many thousands of in-depth business networking product reviews from his lab which have been reproduced globally. Writing for ITPro and its sister title, PC Pro, he covers all areas of business IT infrastructure, including servers, storage, network security, data protection, cloud, infrastructure and services.



