Angry Birds, Squeaky Dolphin, NoseySmurf: The NSA programs you never knew about
IT Pro takes you on a run down of some of the major NSA projects that may have passed you by over the last 12 months

The National Security Agency (NSA), set up to combat foreign and domestic intelligence threats to the US, has had its reputation turned upside down since whistleblower Edward Snowden began to leak details of its clandestine activities.
In the past year, Snowden's leaks have revealed more than 40 separate intelligence campaigns undertaken by the NSA or its UK allies at GCHQ.
Among the most infamous was the news the NSA had been infiltrating the data centres of US technology companies - including Facebook, Microsoft and Google - and snatching user data from the traffic.
Upstream and PRISM, the names of the surveillance operations that conducted those clandestine acts, caused outrage throughout the technology industry and the world. People began to wonder if their data was truly safe in the hands of the big companies and on the internet.
The ripples of that discovery can still be felt today, as companies attempt to side-step their involvement or relocate their services to assuage worried customers.
Yet those two operations were only part of myriad of projects the NSA and GCHQ have undertaken. The details of many more have been released by Snowden over the past year, some of which you might never even have heard of.
Angry Birds

Nowhere is safe from the prying eyes of government agencies, it seems, not even much-loved mobile game Angry Birds.
Get the ITPro. daily newsletter
Receive our latest news, industry updates, featured resources and more. Sign up today to receive our FREE report on AI cyber crime & security - newly updated for 2024.
As soon as a player opened up the game and began their bird-slinging adventures, algorithms within the game's code relayed their age, sex and other information to intelligence agents.
This is according to documents leaked from GCHQ, which revealed how it and the NSA had been working on ways to tap into mobiles and collect data through apps. Not just Angry Birds fell foul of the surveillance program: Google Maps, Facebook, Twitter and LinkedIn were also targeted.
"It effectively means that anyone using a smartphone is working in support of a GCHQ system," a secret 2008 report by the British agency said.
NoseySmurf
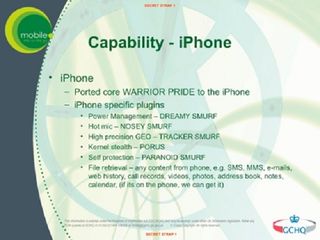
Also known by the names "TrackerSmurf" and "DreamySmurf", the NoseySmurf project tied into the Angry Birds scheme by tapping into mobile phones to scrape data from users.
The NSA spent over $1 billion (580 million) in its search to find more efficient tracking and piggybacking methods for infiltrating targeted devices. In one top-secret presentation, the agency describes a victim uploading an image to Facebook from their phone as a "Golden Nugget!!"
From the simple act of someone uploading a picture to a social media site, later slides say, agents could glean a victim's contacts, location, gender, age, income, ethnicity, education level and even number of children.
HappyFoot

HappyFoot was the codename for an operation designed to track internet users' movements by piggybacking onto their cookies and location data.
When a consumer visits a site cookies are enabled on their computer, allowing the site's company to tailor advertisements to them, something government snoops were keen to exploit.
Slides released by Snowden and published by the Washington Post revealed the NSA had been latching onto these cookies in order to identify possible targets for further hacking operations.
Using a unique cookie from Google called PREF, intelligence agents could pick out one person from a sea of internet data in order to focus on them specifically. The NSA slides indicated that Google complied with this action entirely after being compelled to by the US government.
Squeaky Dolphin

There's a prize for anyone who can understand the reasoning behind this codename. Squeaky Dolphin was an initiative thought up by the UK's GCHQ. It involved tapping into the cables carrying the world's web traffic in order to monitor what people are up to on social media.
Documents leaked to NBC news by Snowden revealed how British spies showed off their new invention to their US counterparts. GCHQ demonstrated how it could monitor YouTube in real time and collect addresses from the billions of videos watched every day.
Analysts demonstrated how, through a central information hub, they could determine which videos were popular in which cities and at what times, as well as what each demographic preferred to click on.
The UK spooks did mention to their allies that this program was for general trends only and not for spying on individuals, but there are as yet unconfirmed rumours GCHQ used the tech to target Twitter users with propaganda.
Gilgamesh
Unfortunately, this operation has nothing to do with the fifth king of Uruk Mesopotamia.
According both to documents released by Snowden and the testimony of a former drone operator, the NSA used telecommunications devices as targets for drone strikes.
Rather than confirming with operatives on the ground, said the whistleblower, the NSA would identify a target based on the geolocation of their phone and order an assassination.
The drone operator was adamant the technology was aiding the War on Terror but that civilians were "absolutely" being killed en masse by the strikes.
Terrorists cottoned on to the NSA's idea, though, and began to mix up their SIM cards to avoid being tracked. Commanders would switch them with footsoldiers and footsoldiers with civilians.
The NSA often located targets based on their activity levels and not on the content of the calls, resulting in, according to the former pilot "death by unreliable data."
EgotisticalGoat

EgotisticalGoat and its sister program, EgotisticalGiraffe, were designed to help facilitate attacks on people using the anonymous network Tor.
Techniques included targeting web browsers like Firefox and giving the NSA full control over a target's computer keystrokes, online activity and files.
The Tor network is relied upon by journalists, activists and campaigners around the world to maintain the secrecy of their communications and avoid reprisals from their respective governments.
The network, oddly enough, is provided with 60 per cent of its funding by the US government.
Agents operating EgotisticalGoat admitted the Tor network was too large for them to completely crack. In one top-secret presentation named "Tor Stinks" it stated "We will never be able to de-anonymize all Tor users all the time ... with manual analysis we can de-anonymize only a very small fraction of Tor users."
With more information to come from Snowden, who claims his leaks to date are just the tip of the iceberg, do we have more cause for concern over our data than ever before? Are all of these operations a gross misconduct or a necessary evil? Let us know what you think by emailing us at comments@itpro.co.uk.




