IT Pro Verdict
WatchGuard’s Firebox T10 sets new standards for affordable small business network security. Don’t be fooled by its size, though, as it packs in a host of enterprise level features.
Pros
- +
Enterprise-level security features; Excellent value; Easy deployment; Fan-less appliance
Cons
- -
Performance slightly lower than quoted
WatchGuard aims to plug the gaps other small business security appliances leave behind. Its latest Firebox T10 offers a similar level of features found in its enterprise UTM appliances allowing SOHOs and remote sites to enjoy equally tough security.
And it won't break the bank either with the starting price of 195 getting you the appliance with firewall, VPNs and a one-year LiveSecurity support subscription. The one year security suite costs 260 and activates a veritable wealth of features.
The suite provides IPS, web content filtering, anti-spam, gateway anti-virus, application controls, HTTPS inspection and WatchGuard's reputation enabled defence. You can also add WatchGuard's optional advanced persistent threat (APT) blocker service and data leak prevention (DLP) with a three year license for the full monty costing only 630.
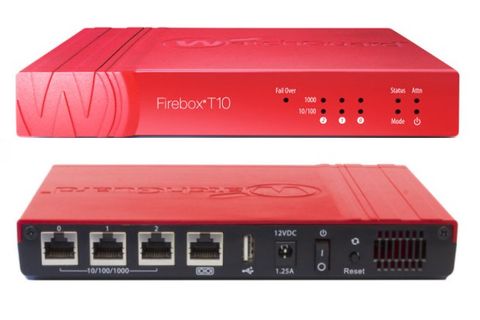
The T10 is a lightweight slab of plastic with three Gigabit ports and is fan-less so it's silent. Installation is swift as you point a web browser at the T10 and follow a quick start wizard which activates a default firewall policy to provide basic protection.
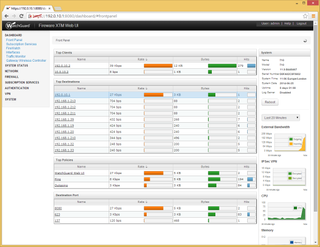
The T10's firmware provides a new dashboard showing more information about network activity and appliance utilisation
A wealth of features
The T10 runs the same FireWare XTM firmware as its bigger brothers which introduces a range of new features. The dashboard is much more informative and provides details of the top clients, destinations, policies and ports.
Performance graphs are provided for all subscription services so you can see what's being allowed and blocked. The graphs can be changed to show activity ranging from the last 20 minutes to 7 days and you can also run manual signature updates from here.
The T10 has the FireWatch feature from WatchGuard's Dimension management software which displays sets of coloured squares where their size indicates the level of activity for sources, destinations, policies, applications and interfaces. MSPs will like the full Dimension product which is included free of charge and runs as a VMware virtual appliance.
The T10 uses proxies for all security services where you create firewall rules for each one that define the interfaces they apply to and the actions they will carry out. There are plenty to choose as you have proxies for HTTP, HTTPS, FTP, SIP, H.323, POP3 and SMTP.
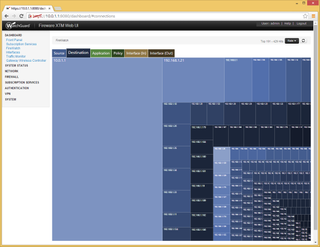
The T10 even includes WatchGuard's FireWatch feature which provides a graphical representation of network activity
Proxies for all
The process of proxy configuration does take some getting used to as you view the predefined actions for each proxy and clone them for use in your policies. For web filtering, you clone the HTTP Client action and assign a profile to it.
The web filter profile uses the Websense cloud service and offers no less than 127 categories to block or allow. An HTTP firewall policy activates it and you can enable IPS on a per policy basis where it applies allow, drop or block actions based on five detected threat levels.
To test the spamBlocker service, we configured the POP3 proxy to tag messages classed as spam, suspect and bulk. After running it for a week using live mail, we saw a high detection rate of 97.5 per cent with no false positives.
Gateway AV scanning is also enabled per policy which you'll need running if you want to apply APT protection. As files come in to the network, it scans them, creates an MD5 hash and checks this with the LastLine cloud service to see if they're known malware.

The optional DLP feature scans web and mail traffic for keywords and can now use custom rules
Application awareness and DLP
WatchGuard's application awareness controls access to hundreds of apps and has eleven entries for FaceBook alone. Link the T10 with AD authentication and you can precisely control social networking on a per user basis and decide who can login, post likes', edit their profile, upload media, play games or chat.
And then there's DLP which can now be used with custom rules. Along with predefined policies for HIPPA and PCI, you can create your own custom ones which run in the HTTP, FTP and SMTP proxies and check for keywords such as credit card or social security numbers.
The T10 has limited internal reporting facilities but it can send its logs to a Syslog server. If you want more you can point the T10 at WatchGuard's Log and Report servers which are part of its Server Center suite and run on a separate Windows host.

The lab's Ixia Xcellon-Ultra NP blades recorded a steady 44Mbits/sec HTTP throughput with UTM enabled
Ixia performance tests
To test the T10's performance, we hooked it up to the lab's Ixia Optixia XM2 chassis and its two Xcellon-Ultra NP blades. Using lightweight UDP packets, raw firewall throughput settled at 170Mbits/sec 15 per cent lower than the claimed 200Mbits/sec.
For HTTP traffic using 512KB web pages we saw a steady firewall throughput of 140Mbits/sec. With the HTTP proxy, IPS and gateway AV enabled this dropped to 44Mbits/sec 11Mbits/sec less the claimed UTM throughput.
Even though performance isn't quite as high as claimed, it's still looks good enough for the T10's target market of small businesses or remote and home offices.
Conclusion
WatchGuard's Firebox T10 may be small in stature but it won't be beaten for its remarkable range of security measures. Its proxy configuration does take some practise to get the hang of but there's nothing else in this market sector that delivers the same level of sophistication at such a low price.
Verdict
WatchGuard’s Firebox T10 sets new standards for affordable small business network security. Don’t be fooled by its size, though, as it packs in a host of enterprise level features.
Chassis: Desktop chassis
Network: 3 x Gigabit (LAN, WAN, OPT)
Other ports: USB2, RJ-45 serial port
Power: External PSU
Management: Web browser
Warranty: 1yr advanced hardware replacement
Dave is an IT consultant and freelance journalist specialising in hands-on reviews of computer networking products covering all market sectors from small businesses to enterprises. Founder of Binary Testing Ltd – the UK’s premier independent network testing laboratory - Dave has over 45 years of experience in the IT industry.
Dave has produced many thousands of in-depth business networking product reviews from his lab which have been reproduced globally. Writing for ITPro and its sister title, PC Pro, he covers all areas of business IT infrastructure, including servers, storage, network security, data protection, cloud, infrastructure and services.