IT Pro Verdict
The CR2500iNG-XP packs plenty of enterprise security measures into a high performance platform and delivers it at a good price. We found it a cinch to deploy and its embedded iView reporting module adds even more value.
Pros
- +
High performance; Easy deployment; Good value; Versatile security measures; Embedded reporting
Cons
- -
Expansion modules not hot-swappable
Top end firewalls cost a king's ransom forcing many mid-sized businesses to accept lower performance and features in their search for value. Cyberoam's latest CR2500iNG-XP aims to gives them the best of both worlds as it offers high performance and extensive security at an affordable price.
The CR2500iNG-XP claims a maximum firewall throughput of over 58Gbps and yet costs under 42,000 with a full three-year TVS (total value subscription) for all services. The Dell SonicWALL SuperMassive 9600, for example, costs up to 30,000 more with only a one-year subscription.
Expansion is also a key feature as the appliance supports up to four of Cyberoam's optional modules. You start with an 8-port Gigabit module and pick and choose from 8-port copper and fibre cold-swap modules or a 4-port 10GbE SFP+ version.

Cyberoam offers a good choice of network expansion modules for the CR2500iNG-XP
Deployment consistency
This 2U rack system comes with a pair of 2.9GHz E5-2667 Xeons, 16GB of DDR3 memory and a 4GB CompactFlash card for Cyberoam's OS. Its 250GB SATA hard disk can be used as an internal email quarantine area and as a report repository for the onboard iView Syslog server.
One feature we like a lot is Cyberoam's total consistency across its entire range of appliances as they all run the same software, offer the same security features and have identical deployment modes. Even if you've only used Cyberoam's little CR10iNG small business appliance, you won't have any problems configuring its bigger brothers.
Installation in the lab was simple as the web interface offers a quick start wizard. The appliance can operate in routed or transparent bridge modes so you can either use it as a firewall or place it behind an existing one.
We chose routed mode and after assigning IP addresses to our LAN and WAN ports, the wizard offered to run in a passive reporting mode or apply one of two predefined security policies. A full complement of ports can make for configuration confusion but we found the port numbering diagrams on the front panel handy.
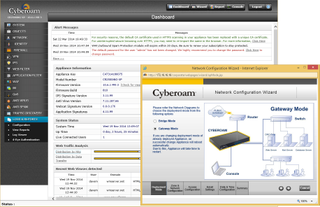
Cyberoams' appliances all use the same setup wizard for swift deployment in bridged or routed modes
Client choices
Cyberoam's identity-based security allowed us to apply policies to users and groups as well as systems. Three types of user are supported where a normal user logs on to the appliance using the Corporate Client utility.
We installed the Windows client on our test desktops where it asked for the IP address of the appliance and user credentials. Mobile users also can get in on the act as along with Linux and Macs, Cyberoam offers free clients for Android and iOS devices.
Clientless users won't have to log on to the appliance but for these you can't apply surfing and data transfer quotas or Internet access time restrictions. The third type of user authenticates with an external directory server and is then automatically logged in to the appliance.
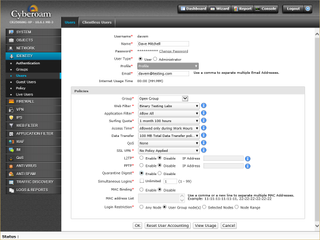
Authenticated users can have their own policies applied for all security services
Security services
Firewall rules use port zones to define sources and destinations plus networks and hosts and apply service filters, blocking actions and time schedules. Within these rules we could also apply web filtering, anti-virus, anti-spam and IPS policies along with internet access limits.
For users and groups, we could apply web filtering, Internet access and bandwidth usage policies to each one. We could also specify data transfer limitations on uploads and downloads and have different values for daily, weekly, monthly and yearly limits.
Web filtering policies can use any of the 85 URL categories provided but it's annoying that the window to display them is so small it can only show three at a time. Even so, we found the web filtering worked very well during testing with very little slipping under its radar.
Anti-spam measures are extensive and for SMTP you can move suspect messages to a quarantine area on the hard disk. A spam digest service is also provided so users that have had messages quarantined can have hourly, daily or weekly reports emailed to them.

The embedded iView server provides a wealth of information and it's included in the price
Embedded iView reporting
Whereas other vendors charge you extra, Cyberoam includes reporting tools and goes one step beyond as they're embedded on the appliance. Its iView Syslog server gathers data directly from the appliances' logs and provides impressive levels of graphing and reporting.
Accessed from the main web console, the iView dashboard opens with a summary of top applications, users and hosts plus source and destination countries. A heap of predefined reports is provided making it easy to pull up details on host activity, general application, web and mail usage, detected attacks and spam, FTP uploads and downloads and even criteria being entered in a range of search engines.
Click on any bar graph and you can drill down for more detailed information. The iView console provides trend reports on the security services plus basic compliance reports for HIPAA, PCI, SoX and more and all can be exported in PDF and Excel formats.
Overall
The CR2500iNG-XP sets a high standard for performance and teams this up with top-notch security features. It's surprisingly easy to install, beats products such as SonicWALL's SuperMassive enterprise boxes on value and Cyberoam's identity based security makes it very versatile.
Verdict
The CR2500iNG-XP packs plenty of enterprise security measures into a high performance platform and delivers it at a good price. We found it a cinch to deploy and its embedded iView reporting module adds even more value.
Chassis: 2U rack
CPU: 2 x 2.9GHz E5-2667 Xeon
Memory: 16GB DDR3
Network: 10 x Gigabit (max 42)
Storage: 4GB CompactFlash, 250GB SATA hard disk
Expansion: 4 x module slots
Power: 2 x hot-plug 500W PSUs
Ports: 2 x USB, RJ-45 console
Management: Web browser, iView
Module options: 8 x copper Gigabit, £923; 8 x SFP Gigabit, £1,352, 4 x 10GbE SFP+, £2,140 (all ex VAT)
Dave is an IT consultant and freelance journalist specialising in hands-on reviews of computer networking products covering all market sectors from small businesses to enterprises. Founder of Binary Testing Ltd – the UK’s premier independent network testing laboratory - Dave has over 45 years of experience in the IT industry.
Dave has produced many thousands of in-depth business networking product reviews from his lab which have been reproduced globally. Writing for ITPro and its sister title, PC Pro, he covers all areas of business IT infrastructure, including servers, storage, network security, data protection, cloud, infrastructure and services.



