IT Pro Verdict
The Performa e9100lite delivers a good range of security features which includes anti-spam measures and mail quarantining. It’s not as powerful as the Dell SonicWALL NSA 2600 but it is better value and easier to deploy.
Pros
- +
Easy deployment; Single price for all subscriptions; Good security measures; Slick reporting; Remote management
Cons
- -
Noisy cooling fans; Weak hardware spec
Panda's GateDefender Performa e9100lite aims to provide complete perimeter security for businesses of up to 250 users. This is more a limitation of the hardware as Panda doesn't enforce per-user licensing and you just pay a yearly subscription fee which activates everything.
And features aplenty there are too as the e9100lite delivers firewalling, support for IPSec and SSL VPNs, anti-virus, anti-spam, web content filtering and application controls. Its mirrored hard disks serve as a web cache and spam quarantine area and Panda provides some cunning wireless security features as well.
The e9100lite has a modest hardware spec comprising an elderly 2.6GHz dual-core Pentium E5300 and 2GB of DDR2. We also found the cooling fans are very noisy making it a poor partner in an office environment.
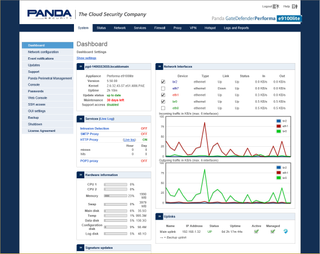
Panda's dashboard view keeps you posted on proxy and appliance status plus traffic throughput
Proxies for all
The eight Gigabit ports can be used to provide LAN, WAN or DMZ duties. For installation we just hooked a system up to the first port, faithfully followed the quick start wizard and had it up and running with secure Internet access inside 15 minutes.
We particularly liked Panda's colour coordination as it uses green, red, orange and blue zones for trusted, Internet, DMZ and wireless services. This made light work of deciding where to apply our security policies as we could choose which physical ports were members of each coloured zone.
Proxies are used throughput Panda's security policies and control HTTP, HTTPS, SMTP, POP3 and FTP traffic. You have non-transparent and transparent proxies for HTTP and we plumped for the latter as it avoided making any changes on our users' browser settings.
Profiles are used to assign filtering policies to sources and destinations and enforce authentication using the local appliance, Active Directory, LDAP or RADIUS. For web filtering, Panda offers five general URL categories covering themes such as parental control and security and within these you have a total of 83 sub-categories so filtering can be easily fine-tuned.
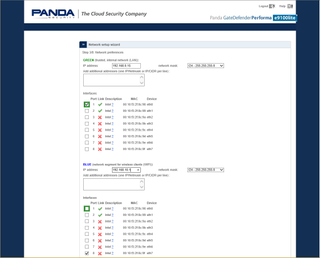
Panda's colour schemes made it easy for us to assign policies to the correct ports
Anti-spam and wireless security
The POP3 proxy is easy to configure where it applies anti-virus measures and the SpamAssassin service to inbound mail. However, it can only tag the subject line of suspect spam messages and can't move them to the quarantine area.
The SMTP proxy uses the more sophisticated CommTouch hosted service but can only be applied to mail traffic being passed to an internal mail server. However, along with virus and spam checking, it can send suspect messages to the hard disk quarantine area for further examination.
For wireless network security you simply plug an AP or a switch carrying wireless traffic into the ports placed in the blue zone. For secure Internet services, all proxies can be applied to the blue zone and the firewall configured to allow wireless traffic only between blue and red zones.
The Hotspot feature is a standard service across all GateDefender appliances and supports access and billing controls. You can also use it to redirect wireless users to a login web portal complete with AUP.
Performance surprises
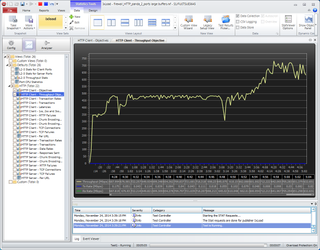
For performance testing we used the lab's Ixia Xcellon-Ultra NP load modules and IxLoad control software. Prior to starting we disabled the appliance's web caching by adding the Ixia's virtual servers to the proxy's non-cache list.
We're not sure how Panda tests its appliances but even with caching disabled we saw significantly better results than those claimed. With the HTTP proxy disabled, we saw an average firewall throughput of 915Mbits/sec - 14 per cent higher than Pandas' figures.
Enabling the proxy with a basic non-filtering policy saw throughput drop to 480Mbits/sec and with AV scanning enabled this fell further to 230Mbit/sec. IPS takes its toll as with this enabled, IxLoad recorded an average HTTP throughput of 180Mbits/sec still nearly twice Pandas' claims.
To check the appliance's caching efficacy, we reran the test with the proxy only enabled and confirmed our 480Mbit/sec results. Halfway through the test, we enabled the cache for all web traffic and saw the throughput graph jump rapidly up to around 650Mbits/sec.
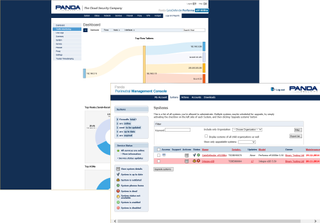
Along with good on-board reporting, the appliance can be managed remotely using the PMC portal
Perimetral controls and reporting
Panda's Perimetral Management Console (PMC) will appeal to larger businesses and MSPs with multiple appliances spread over different locations. To use the PMC web portal we just needed to register our appliances with it during the setup phase. The portal opens with a list of assigned appliances each with status icons and remote access facilities for management and updates.
On-board reporting facilities are good as the appliance's web interface provides a dashboard overview of all activity and a wealth of graphs for the services, proxies and firewall. The traffic monitoring page provides some slick graphs showing flows and top hosts while live logs for all proxies let us keep a close eye on the action.
Conclusion
The e9100lite is better value than the Dell SonicWALL NSA 2600 as although this appliance is much more powerful, a one-year Total Secure bundle and anti-spam subscription pushes costs to nearly 3,000. What we also like about the e9100lite is its easy deployment, the port zoning features and its vendor agnostic wireless security measures.
Verdict
The Performa e9100lite delivers a good range of security features which includes anti-spam measures and mail quarantining. It’s not as powerful as the Dell SonicWALL NSA 2600 but it is better value and easier to deploy.
Chassis: 1U rack
CPU: 2.6GHz dual-core Intel Pentium E5300
Memory: 2GB DDR2
Storage: 2 x 250GB SATA hard disks
Network: 8 x Gigabit (LAN, WAN, DMZ)
Other ports: 2 x USB 2, RJ-45 serial, VGA
Power: Internal PSU
Management: Web browser
Options: Further yearly subscriptions, £1,408 ex VAT
Dave is an IT consultant and freelance journalist specialising in hands-on reviews of computer networking products covering all market sectors from small businesses to enterprises. Founder of Binary Testing Ltd – the UK’s premier independent network testing laboratory - Dave has over 45 years of experience in the IT industry.
Dave has produced many thousands of in-depth business networking product reviews from his lab which have been reproduced globally. Writing for ITPro and its sister title, PC Pro, he covers all areas of business IT infrastructure, including servers, storage, network security, data protection, cloud, infrastructure and services.


