NSA & GCHQ SIM card hack: Gemalto denies encryption keys stolen through hack
Special mobile unit was set up in 2010 to steal encryption keys

SIM card maker Gemalto has shared details of its investigation into claims British and US securities services hacked the company to steal billions of encryption keys.
Privacy International blasts security services
"GCHQ has lost it's way. In stealing the SIM card encryption keys of millions of mobile phone users they have shown there are few lines they aren't willing to cross," the charity told IT Pro.
"Hacking into law-abiding companies, spying on their employees and stealing their data should never be considered 'fair game.'
"The mentality of 'Act first, worry about the law later' has to come to an end. Unrestrained, unregulated Government spying of this kind is the antithesis of the rule of law and they must be held accountable for their actions."
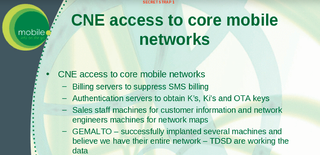
The two agencies are said to have joined forces to set up a specialist Mobile Handset Exploitation Team (MHET) in April 2010, documents by The Intercept revealed. The unit's mission was to target vulnerabilities in mobile devices.
Operatives worked to infiltrate Dutch company Gemalto, which produces 2 billion SIM cards a year and serves 450 telecoms operators across the globe, it was claimed.
Get the ITPro. daily newsletter
Receive our latest news, industry updates, featured resources and more. Sign up today to receive our FREE report on AI cyber crime & security - newly updated for 2024.
A top secret slide (below) confirmed the NSA and GCHQ had gained access to Gelmato's network and mined the private communications of engineers and sales employees.
The claims are the latest in a long line of revelations to have been made public by NSA whistleblower Edward Snowden.
By stealing encryption keys, the intelligence agencies were able to monitor mobile communications without approval from telecom companies and foreign governments, all without being traced.
In a statement published on 25 February, the organisation said it has reason to believe the NSA and GCHQ were behind a series of attempts made in 2010 and 2011 to hack into the company and its network.
"At the time we were unable to identify the perpetrators but we now think they could be related to the NSA and GCHQ operation," the statement reads.
"These intrusions only affected the outer parts of our networks - our office networks - which are in contact with the outside world.
"The SIM encryption keys and other customer data in general, are not stored on these networks," the statement added.
Therefore, it denied claims the security services were able to steal the SIM encryption keys because the NSA and GCHQ appear to have only succeeded in breaching its office networks.
Instead, Gemalto's investigation into the matter has suggested the NSA and GCHQ may have targeted other parts of its SIM card supply chain to get access to the encryption keys, rather than via its own network.
Furthermore, it also denies that it ever sold SIM cards to four out of the 12 operators listed in the leaked documents.
Gemalto described the attacks as as "serious and sophisticated", but said no signs of malicious activity were observed anywhere else in its networks.
"No breaches were found in the infrastructure running our SIM activity or in other parts of the secure network which manage our other products such as banking cards, ID cards or electronic passports," the statement continued.
"We are conscious that the most eminent state agencies, especially when they work together, have resources and legal support that go far beyond that of typical hackers and criminal organisations.
"And, we are concerned that they could be involved in such indiscriminate operations against private companies with no grounds for suspicion," the statement concluded.
When the allegations first came to light last week, Gelmato said in a statement that the security services appear to have tried to reach as many mobile phones as possible.
"We cannot at this early stage verify the findings of the publication and had no prior knowledge that these agencies were conducting this operation," the firm said.
"We take this publication very seriously and will devote all resources necessary to fully investigate and understand the scope of such sophisticated techniques."
This article was originally published on 25/2/15 and updated on the same day to include details of Gemalto's investigation.




