Kaspersky
Latest about Kaspersky

One quarter of all data breaches due to employees swerving security policies
By Solomon Klappholz published
News There are a concerning number of cyber security incidents caused by employees acting deliberately

80% of C-suites aren’t acting on worries that workers already use generative AI
By Rory Bathgate published
News The disconnect between fears around generative AI and a willingness to use it in place of employees could have profound implications for business security

Kaspersky traces spyware attack on staff iOS devices back to 2019
By Rory Bathgate published
It's currently unclear who is behind the spyware attack on the Russian-based cyber security firm

US considers fresh punishments for Kaspersky on national security grounds
By Connor Jones published
News The embattled Moscow-based company has fended countless allegations of Kremlin collaboration for more than a decade

Free decryptor released for Conti ransomware variant infecting hundreds of organisations
By Ross Kelly published
News Hundreds of organisations and state institutions are believed to have been impacted by the strain

'CryWiper' trojan disguises as ransomware, says Kaspersky
By Rory Bathgate published
News The destructive wiper mocks up files as if encrypted, while in reality overwriting all but core system files

Kaspersky finds most effective phishing emails imitate corporate messages, delivery notifications
By Rory Bathgate published
News Almost one in five employees clicked links in business related emails, but most emails containing threats or promising money were identified as phishing
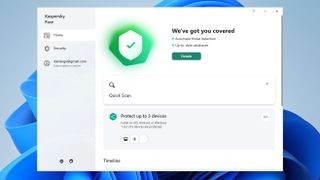
Kaspersky Free review: Effective and lightweight – everything you want from a free antivirus solution
By Darien Graham-Smith published
Reviews It’ll be a real shame if politics means people missing out on this top-class security tool
Get the ITPro. daily newsletter
Receive our latest news, industry updates, featured resources and more. Sign up today to receive our FREE report on AI cyber crime & security - newly updated for 2024.




