What is phishing?
From banking scams to industrial espionage, we look at why phishing is so lucrative
With numerous emails flooding in from all sorts of sources every day, it’s a tiring job to scrutinise each one and treat it as guilty until proven innocent. Unfortunately, not doing so is why phishing remains such a lucrative hacking technique.
Phishing is an attack method most commonly delivered through emails that try to trick the victim into believing that a trusted source needs something from you, whether that’s money, identifiable data, or login credentials.
While it has long been the most common and costly attack method, phishing has become particularly favoured during the pandemic, with the number of attacks increasing by 220% in 2020.
Opening malicious email attachments are a simple method of attack, but it keeps proving to be one of the most efficient. This backs up the conclusion that many organisations are reaching - that the human element of cyber security is the weakest link.
Here's what you need to know about some of the types of phishing attacks you may come across and the motivations of the attackers.
The first phishing attacks
While a theoretical phishing technique was first described in 1987, this type of attack only really started to gain popularity in the 1990s, with the advent of the consumer internet.
One of the earliest examples of phishing was known as AOHell and was a customer service ruse. This hacking tool targeted AOL users and allowed the attacker to masquerade as a customer service representative. The target user would be encouraged to hand over their password if they did, then the attacker would be able to use their account for nefarious purposes.
Get the ITPro. daily newsletter
Receive our latest news, industry updates, featured resources and more. Sign up today to receive our FREE report on AI cyber crime & security - newly updated for 2024.
This element of using underhand tactics remains the defining feature of phishing, although the number of types and techniques has expanded significantly.
How to spot a phishing attack

Most users will encounter phishing attacks in the form of malicious emails. As is shown in the image above, many of these will be caught by the service provider's built-in filters, which will alert the user to suspicious content or recent attacks associated with the sender's address. However, some malicious emails will slip through the net, so it's important to always be suspicious of any unexpected email, especially from those purporting to be from companies that you have had no dealings with.
Unusual sender address
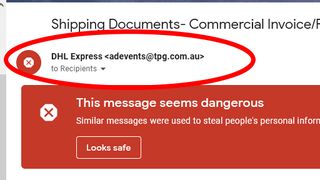
An email from a legitimate company will normally use a fairly standard address - something that is representative of the brand. Although sophisticated attacks will try to masquerade as the company they're imitating, such as using PayPal.net instead of PayPal.com, many will forgo this effort and use clearly suspicious email addresses with the hope the victim won't notice. As you can see in the image above, this particular email claims to be from DHL Express, but the message has been sent from an entirely unrecognisable address.
Spelling mistakes, grammatical errors, strange phrasing

Legitimate emails will normally have been put through many layers of proofing and checks prior to being sent, especially if they are automated. This means that spelling and grammatical errors, or sentences that just don't sound quite right, should be an instant red flag. Occasional spellings mistakes are understandable, especially if the email does not appear to be automated, but you should be suspicious of glaring errors nonetheless.
As you can see in the image above, the email comes with an official-sounding sign-off that just doesn't sound right.
Vague information or requests

Companies will typically try to personalise their customer correspondence, usually by addressing the email to a specific first name taken from account information, or by using very specific information from a recent order. Another red flag, then, is the lack of this personalised information, especially when the email is addressed to a 'Sir/Madam' or 'Recipient', or if the email mentions vague references to a recent order. Malicious emails will use this lack of specific information to encourage a secondary action, whether that's clicking on a link or opening an attachment.
COVID-19 phishing attacks
Hackers were quick to jump on the opportunity of the pandemic as businesses struggled to find their footing with new ways of working and securing employees.
Much of the communications themselves have also centred around the coronavirus, with hackers playing people's fears of the virus to entice clicks on malicious emails.
In May last year, Microsoft warned of a "massive" phishing campaign that used coronavirus-themed emails to deliver attachments containing malicious Excel 4.0 macros. These malware-laced emails, which had the subject line “WHO COVID-19 SITUATION REPORT," claimed to come from the Johns Hopkins Center for Health Security and showed a graph purporting to display coronavirus cases in the US.
In addition, Google has recorded a huge surge in phishing emails sent during the pandemic. The company said that it's now blocking upwards of 100 million phishing emails on a daily basis, almost 20% of which were related to COVID-19. These emails, which often impersonate government organisations and company clients, have been designed to target employees working from home, small businesses, and organisations impacted by the government-induced lockdown.
It's not just the everyday employees working from home who are being targeted by phishing emails. The NHS has also been flooded with emails during the crisis, with NHS staff receiving some 43,108 malicious emails since the beginning of the pandemic, half of which were delivered in March alone.
The World Health Organization also reported a five-fold increase in phishing attacks in the first few weeks of the outbreak. These attacks were aimed at getting confidential information about the pandemic or disrupting those trying to combat it. This has evolved to hackers also reportedly trying to phish companies making vaccines.
Financial phishing attacks
Financially motivated phishing attacks have been used for a long time and take on many different guises.
Many of us will be familiar with the so-called Nigerian Prince scam emails, whereby the victim is contacted by a person alleging to be a representative of a Nigerian prince who, for whatever reason, wants to transfer some of his wealth out of the country and will give the victim a cut of the money if they let the scammer use their bank as a conduit. Other variations include the death of a long-lost relative or, more recently, a friend or family member who has been robbed while on holiday and needs an emergency loan.
Normally, this scam results in a loss of money - not because bank details are handed over, but because the victim is asked to pay money out to the scammer first, who they never hear from again.
This is a very basic form of a financial phishing attack, but others are much more sophisticated. Scammers are sending out increasingly well-crafted emails that appear to be genuine messages from real banks. This type of attack is aimed at getting a user to enter all their bank or credit card details into a website accessed through a link in the phishing email that looks like the genuine article but is in fact owned by the criminals. Once that is done, the phisher can use the details as if they were the legitimate cardholder or bank customer.
Account takeover
Account takeover is what the first phishing attacks were geared towards - gaining access to another person's online account, whether it's on social media, email, a forum or something else and then taking control of it.
This is typically done via a malicious link sent in a legitimate-looking an email, instant message or direct message. Once the user clicks on it, they will be taken to a realistic-looking website operated by the attackers and, much like the banking attacks mentioned above, asked to enter their username and password.
The purpose of an account takeover could be to send spam from that email address or social media account; to find out further information about the person, including financial information or other sensitive data; or as a form of protest. Rival ideologies at the fringes of politics have been known to take over and shut down the accounts of their opponents, for example.
Cyber-espionage
This category covers both industrial espionage and state-level snooping. In both cases, the objective is to gain information on your rival with the aim of outmanoeuvring them or, in some cases, sabotaging them.
In this case, the email is normally crafted to look like it came from a supplier or perhaps a senior person within the company and has a sense of urgency. This, it's hoped, will make the recipient of the email more likely to respond with the information quickly, suppressing any doubts if they do arise.
This can be part of a much longer campaign that involves many other types of cyber attack like spyware and specially created malware to harm industrial machinery or national infrastructure.
Phishing subtypes
Under the umbrella of "phishing", security researchers have identified a number of sub-groups that are even more targeted in their approach, with the two most common being spear-phishing and whaling.
Spear phishing
Spear phishing is a phishing campaign that targets a specific individual or company. This technique requires a bit more effort on the part of the cyber criminal, as they need to do more background research in order to create a personalised phishing email. According to research, 88% of organisations worldwide reported spear-phishing attacks in 2019.
Whaling
Whaling is like spear-phishing, but it's even more targeted, focusing on the likes of CEOs and CFOs within a business. These emails are crafted to look like an urgent item a senior person within a business must look at, such as a customer complaint or a court subpoena. The scams often then demand the transfer of a large sum of money.
The Symantec report said that "these scams can be damaging as they require little technical expertise but can reap huge financial rewards for the criminals and significant losses for the companies involved. For example, early in 2016, an Austrian aerospace company fired its CEO after it lost almost (USD) $50 million to BEC scammers".
Most common phishing emails of 2022
Research from cyber security firm Aware Force has revealed the seven most common types of phishing attacks that have hit businesses so far in 2022.
- The most common type of phishing involved emails sent claiming to be collecting cash for victims of the Ukraine war
- Fake streaming links for upcoming films: Spiderman ‘No Way Home’ was one of the most common subjects
- Targeting social media users with fake password updates, claiming they need to be reset in order to harvest login credentials
- Fake malware alerts: criminals would encourage victims to call a phone number for the operator to ‘fix’ their machine
- Emails claiming to alert users to suspicious activity on their account with a widely used company, such as Disney and ESPN
- Kinetic phishing: malicious USB drives mailed through victims’ doors encouraging them to be used in order to claim a prize or gift voucher
- QR code fraud: scammers placed QR codes leading to payment portals on fake parking tickets
Working professionals should also be especially aware of any emails purporting to come from LinkedIn since Check Point Research announced that the business-oriented social media network was the most-spoofed brand by cyber criminals for the first quarter of 2022.
More than half of phishing emails (52%) used LinkedIn branding, according to Check Point Research which represents a huge increase from the 8% of emails using the company branding in the previous quarter.
Trend: Ice phishing
Microsoft’s 365 Defender Research Team also detailed a novel form of phishing called ‘ice phishing’ earlier this year, a technique that involves manipulating the processes involved in completing blockchain transactions.
The idea is that these attacks will become more popular as blockchain technology starts to entrench itself deeper into everyday life, through the use of cryptocurrencies and non-fungible tokens (NFTs), for example.
Ice phishing attacks have already been observed during a December 2021 hack on the Badger DAO platform, leading to large amounts of digital assets, worth massive sums, stolen from users. Ice phishing involves tricking a user into signing over the transaction approval to the attackers, and then manipulating the platform to modify the transaction, changing the target wallet address to their own.
Observed success with ice phishing is still low, given its technical complexity and reliance on Web 3.0 technology, but it’s certainly one to watch out for as businesses increasingly embrace the latest generation of internet technology.

Clare is the founder of Blue Cactus Digital, a digital marketing company that helps ethical and sustainability-focused businesses grow their customer base.
Prior to becoming a marketer, Clare was a journalist, working at a range of mobile device-focused outlets including Know Your Mobile before moving into freelance life.
As a freelance writer, she drew on her expertise in mobility to write features and guides for ITPro, as well as regularly writing news stories on a wide range of topics.