The cyber security threat in six charts
What happens when UK firms experience security attacks?

The threat of cyber security is unquestionably growing more serious over time. The impact of attacks on businesses can be devastating, and for many, the source remains unknown - as many as 35% of attacks on UK-based organisations are from an unknown source.
The majority of organisations consider dealing with cyber threats, and ransomware in particular, as a high priority, but many lack confidence in their ability to respond to a successful attack.
These charts are from two reports by Malwarebytes. The first is a report into Cybercrime tactics and techniques: 2017 state of malware', evaluating the key findings and cybercrime trends in 2017. The second is a survey on 'The Second Annual State of Ransomware' undertaken in the United Kingdom as part of a larger survey of organisations across the world on ransomware and other critical security issues. It was conducted with small to mid-sized businesses during June 2017, with individuals who are responsible for or knowledgeable about cyber security issues at 175 UK organisations.
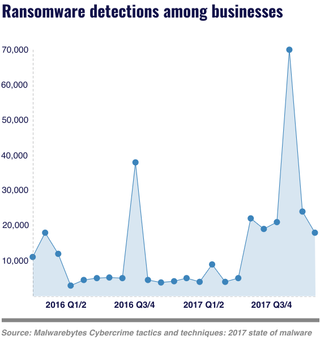
Ransomware attacks saw a serious spike in Q3 of 2017
Statistically, 2017 was a banner year for ransomware. According to the report, business and consumer ransomware detections have increased 90% and 93% respectively, largely because of families like WannCry, Locky, Cerber and Globelmposter. In fact, the monthly rate of ransomware attacks against businesses increased up to 10 times the rate of 2016.
The summer months brought in a flood of ransomware infections from a couple of new players. Between July and September 2017, there was a 700% increase in ransomware, with Globelmposter and WannaCry making up most of that statistic.
In addition, nearly seven percent of all attacks against businesses in September 2017 involved ransomware, compared to the average rate of ransomware attacks in 2016, which totalled 1.11%
Get the ITPro. daily newsletter
Receive our latest news, industry updates, featured resources and more. Sign up today to receive our FREE report on AI cyber crime & security - newly updated for 2024.

Malware infiltration through email is the top security concern
For 85% of organisations, the top concern is malware infiltration through email, closely followed by phishing through email. For both of these attacks, email servers only form part of the defence, and businesses are reliant on staff being able to identify suspicious emails.

Almost all UK organisations have experienced security attacks
Most organisations in the UK have experienced various types of security attacks and data breaches over the past year, with many facing some type of security-related incident on a more than monthly basis. But with 44% of decision-makers being fairly or very confident that they can stop attacks, it looks like the defences are holding for now.

Most ransomware incidents have affected just the endpoint
Of the most serious ransomware attacks that have hit organisations, 57% have affected just an organisation's endpoint. However, for 2% of companies, the impact of ransomware has been devastating, affecting every device on the corporate network.

Ransom demands from cyber criminals are fairly small
Over half of ransom demands from cyber criminals to small and mid-sized businesses are for less than $1,000. However, there are still a fair proportion of criminals who ask for much larger sums, with 42% asking for more than $1,000 and 3% demanding a whopping $50,000 to $150,000 to release files. Survey respondents reported that more than two in five UK organisations opted to pay the ransom demand in the most serious ransomware attack.

Email security is the top process in place to address cyber attacks
Most of the surveyed organisations in the UK have deployed email security to address malware and phishing attempts. They have also implemented regular, on-premises data backups so that they can restore affected machines to a known good state as quickly as possible. Many organisations have also implemented network segmentation, used outsourced security providers, on-premises ransomware-detection solutions, and regular cloud-based backup capabilities to further counter threats.
Esther is a freelance media analyst, podcaster, and one-third of Media Voices. She has previously worked as a content marketing lead for Dennis Publishing and the Media Briefing. She writes frequently on topics such as subscriptions and tech developments for industry sites such as Digital Content Next and What’s New in Publishing. She is co-founder of the Publisher Podcast Awards and Publisher Podcast Summit; the first conference and awards dedicated to celebrating and elevating publisher podcasts.