The rise of ransomware as a service
Ransomware is no longer just for hackers - it's available off-the-shelf

Ransomware as a service (RaaS) is designed so that anyone, no matter how limited their programming knowledge, can get started in cybercrime. Professional criminals write and package the code before making it available for amateurs to download and use, flooding the market with new ransomware strains in the process.
Read Kaspersky's free security bulletin The ransomware revolution' for a deep-dive view of ransomware and other security threats
While this is not a new trend, the model is developing rapidly, with increasing numbers of ransomware creators offering their malicious products on demand'. This approach has proved immensely appealing to criminals who lack the skills, resources or inclination to develop their own.
This makes ransomware very cheap to download and easy to spread, compared to other types of malware and cyber attacks which require a higher level of programming and distribution knowledge. It is this growth in RaaS platforms which is likely to be one of the primary drivers behind the huge spike in ransomware attacks over the past 12 months.
Notable examples which appeared last year and use this model are Petya/Mischa (see below) and Shark ransomware, which was later rebranded under the name Atom and offered a high 80% share on ransom payments. Other popular tools like Satan claim to enable distribution of ransomware in under a minute.

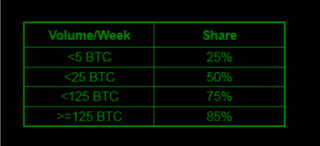
The business model for RaaS is a simple, franchise-like deployment model. Instead of writing and deploying their own ransomware software, a criminal will sign up to a traditional commission-based arrangement. One example is Peyta ransomware (see table below); if a partner makes 125 Bitcoins a week, they will walk away with 106.25 Bitcoins after commission. Some even get to see an estimate of their potential earnings before they sign up.
Get the ITPro. daily newsletter
Receive our latest news, industry updates, featured resources and more. Sign up today to receive our FREE report on AI cyber crime & security - newly updated for 2024.
There is also often an initial usage fee. Someone looking to use the Stompado ransomware, for example, needs to spend just $39 to get started. Other RaaS authors instead opt to take a cut of each ransom, incentivising a higher volume of attacks.
Have you protected your infrastructure from the risks of ransomware? Keep up to date with current threats to businesses with Kaspersky's security whitepaper detailing trends from the past year.
With other criminals offering their services in spam distribution and ransomware notes, it's no longer difficult for an amateur attacker to get started.
Typical antivirus solutions are designed to stop known attacks, so unfortunately are relatively ineffective against such a rapidly growing number of new ransomware strains. Using a reliable security solution, particularly one with a dedicated ransomware feature is an important way to keep your data and devices secure.
Businesses should also take steps to educate employees and IT teams about suspicious emails, and what to do in the event of falling victim to a ransomware attack. IT teams can take steps such as keeping sensitive data separate, restricting access and backing up everything regularly to mitigate the effects of a potential ransomware attack.
Petya RaaS screenshots via Kaspersky Security Bulletin 2016, The Ransomware Revolution, p13
Esther is a freelance media analyst, podcaster, and one-third of Media Voices. She has previously worked as a content marketing lead for Dennis Publishing and the Media Briefing. She writes frequently on topics such as subscriptions and tech developments for industry sites such as Digital Content Next and What’s New in Publishing. She is co-founder of the Publisher Podcast Awards and Publisher Podcast Summit; the first conference and awards dedicated to celebrating and elevating publisher podcasts.