IT Pro Verdict
We didn’t think Adaptive Defense 360 could get any better but Panda proved us wrong - this latest version is packed to the gills with new features. Its improved management, remarkable range of endpoint protection services and top value ensures it earns a well-deserved IT Pro Editor’s Choice Award.
Pros
- +
Swift installation
- +
Centralised management
- +
Wealth of malware protection features
- +
Patch management that works
- +
Great data control services
- +
Web portal occasionally slow to update
Cons
Panda’s Adaptive Defense 360 (AD360) takes cloud-hosted security to the next level, combining a wealth of endpoint protection features with data control, encryption and patch management tools. This makes it appealing to businesses with GDPR compliance on their minds, as they can protect endpoints from malware, keep them updated with the latest patches and stop data containing PII (personally identifiable information) from leaking, all with a single tool.
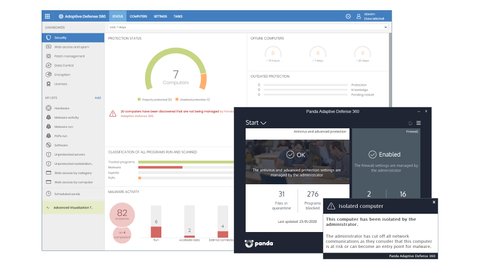
AD360’s advanced protection module analyses and classifies every application being run on Windows endpoints and only blocks those it doesn’t know about. It doesn’t stop them from running permanently though; Panda’s cloud service checks the app’s security posture in the background and, if it’s deemed to be safe, will instruct the endpoint client to allow it through.
AD360’s endpoint protection features are extensive, including file, email and web antivirus, a firewall, web filtering and removable device controls for Windows systems. Exchange servers are supported too, and AD360 provides separate antivirus, antispam and attachment content filtering components.
The data protection module scans protected endpoints using machine learning algorithms and regular expressions to detect PII content in a wide range of file formats. It keeps track of all activity and can tell you what each user has been doing with these files such as opening, editing and renaming them, sending and receiving them via email or copying them to removable media.
Panda Adaptive Defense 360 review: Deployment
Deployment is undemanding, thanks to endpoint agents for Windows, macOS, Linux and Android, which can be downloaded from the portal or emailed as a web link. A quicker option for installation on the LAN is to install the agent on one machine first and designate it as a discovery computer.
This scans the network and presents a list of all discovered devices, where you select them and push the agent out remotely. Either way, it only took us a minute to load it on each of our Windows 10 clients after which it contacted the cloud service and applied all our predefined settings.
All endpoints are dropped into a default group with a base security profile for immediate protection but you can easily create your own groups, each with a set of custom profiles. These are used to define active security services, firewall rules and update frequency while web filtering offers over 60 categories to block or allow and can use daily schedules to determine when it was active.
Initially, you run the advanced protection in ‘audit’ mode where it gathers information about your everyday apps. When you’re ready, you can set it to ‘hardening’ mode which will block unknown external programs until they’ve been assessed, while the ‘lock’ mode includes all local apps as well.
Panda Adaptive Defense 360 review: Patch management
Patch management is an optional feature and requires the endpoint protection or adaptive defense components to be licensed. As with Avast’s Business Patch Management (BPM), it can’t be run on its own but Panda has made a far more professional job of implementing it.
Panda requires Windows automatic updates to be disabled and, unlike Avast’s BPM, it’s all done for you. When creating a patch management policy, you can request automatic updates to be disabled and we found it worked perfectly on all our Windows 10 test clients with no manual intervention required.
Profiles determine a scan frequency of between one hour and once a day and after scanning all our clients, Panda created a list of available updates separated into five criticality levels along with non-security related and service pack groups. Tasks are used to deploy patches and include client groups, a schedule, selected patch groups and third-party products from the software inventory that you also want patched.
Panda then just gets on with the job of patching and provides a task status view that shows which clients are patched and those in progress. If users try to reboot their system during this process, they’ll receive a pop-up message advising them that patching is in progress.
Panda Adaptive Defense 360 review: Data control
The data control component is fully integrated into the web portal and uses profiles to determine what it should search for. To scan and index Office documents, each Windows endpoint requires the Microsoft Filter Pack 2.0 installed which we downloaded straight from the AD360 portal.
You can choose to index only text files but if you opt to index everything on each client, the first run will take many hours and possibly a day. Even so, it’s worth the wait as Panda came back with a heap of valuable information about files residing on our clients that contained PII.
The portal separates them into groups such as personal ID, passport, credit card and phone numbers, email addresses plus bank account details and clicking on a graph category takes you to a list of clients with details of the exact file locations. We could run advanced searches on selected clients to look for keywords and phrases in a range of file types and use the portal to remotely delete unwanted files.
The advanced visualization tool takes this further as it’ll tell you what actions have been carried on these files and when, the application that accessed them, the user responsible and exfiltration risk levels. It provides a lot more information than this though, as it can present detailed reports and graphs on security incidents, malware detections and app controls.
Panda Adaptive Defense 360 review: Verdict
Panda’s Adaptive Defense 360 is a clever cloud security solution that delivers a wealth of endpoint protection features at a great price. It’s easy to deploy and manage, offers sophisticated data control features and whereas other security vendors stumble with patch management, Panda has perfected it.
Dave is an IT consultant and freelance journalist specialising in hands-on reviews of computer networking products covering all market sectors from small businesses to enterprises. Founder of Binary Testing Ltd – the UK’s premier independent network testing laboratory - Dave has over 45 years of experience in the IT industry.
Dave has produced many thousands of in-depth business networking product reviews from his lab which have been reproduced globally. Writing for ITPro and its sister title, PC Pro, he covers all areas of business IT infrastructure, including servers, storage, network security, data protection, cloud, infrastructure and services.