Intel security flaws put laptops, servers and storage at risk of hacking
Bugs in Intel's firmware allow remote code execution, data exfiltration and more
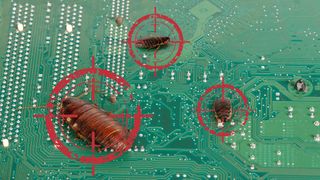
Bugs in the underlying firmware of multiple Intel chip families have left laptops, servers and storage appliances vulnerable to a number of security vulnerabilities, the company has admitted.
The silicon giant has confirmed reports from third-party security researchers that flaws in its chips' management and administration functions could potentially allow hackers to execute code, exfiltrate confidential data and more.
Intel launched a full internal review of its source code after it was alerted to the issues, finding that bugs in affected systems could allow attackers to "load and execute arbitrary code outside the visibility of the user and operating system [and] cause a system crash or system instability".
The flaws affect a wide variety of chip families, including 6th, 7th and 8th Generation Intel Core processors, Intel Xeon E3-1200 v5 and v6 processors, Intel Xeon Scalable processors, Intel Xeon W processors, Intel Atom C3000 processors, Apollo Lake Intel Atom E3900 series, Apollo Lake Intel Pentiums, and Celeron N and J series processors.
This covers everything from laptops and 2-in-1s, all the way up to high-end servers and storage appliances. The company has released a free detection tool, which users and sysadmins can run to identify vulnerable machines. IT Pro has contacted Intel to try and determine the number of affected systems.
Three elements of Intel's firmware are vulnerable: the company's Management Engine (ME) Server Platform Services (SPS) and Trusted Execution Engine (TXE). The Management Engine runs underneath the OS, and is used by admins to remotely access a system for maintenance and management tasks. The Server Platform Services feature is based on the ME and offers similar features for server products, while the TXE deals with hardware authentication.
The ME allows anyone with the appropriate credentials to control desktops, make changes to the system's settings and configurations, and even reinstall the OS. This makes it a very useful tool for IT staff at large companies with multiple offices, but it also means it holds a huge amount of power that hackers could take control of.
Get the ITPro. daily newsletter
Receive our latest news, industry updates, featured resources and more. Sign up today to receive our FREE report on AI cyber crime & security - newly updated for 2024.
Because it runs underneath the OS, the ME is invisible to any antivirus systems or hypervisors installed on the machine. Coupled with its highly-privileged status, this means that a compromised ME could be used to install malware, among other troubling things.
A security advisory issued by Intel stated that 80% of the ten CVEs relating to the flaws are designated as high-severity, with buffer overflows and privilege escalations seen throughout.
"Based on the items identified through the comprehensive security review," the advisory read, "an attacker could gain unauthorized access to platform, Intel ME feature, and 3rd party secrets protected by the Intel Management Engine (ME), Intel Server Platform Service (SPS), or Intel Trusted Execution Engine (TXE)."
Intel has confirmed to IT Pro that patches are now available for affected systems, and the company advised that they should be installed as a matter of urgency.
"We worked with equipment manufacturers on firmware and software updates addressing these vulnerabilities," Intel said, "and these updates are available now. Businesses, systems administrators, and system owners using computers or devices that incorporate these Intel products should check with their equipment manufacturers or vendors for updates for their systems, and apply any applicable updates as soon as possible."
Adam Shepherd has been a technology journalist since 2015, covering everything from cloud storage and security, to smartphones and servers. Over the course of his career, he’s seen the spread of 5G, the growing ubiquity of wireless devices, and the start of the connected revolution. He’s also been to more trade shows and technology conferences than he cares to count.
Adam is an avid follower of the latest hardware innovations, and he is never happier than when tinkering with complex network configurations, or exploring a new Linux distro. He was also previously a co-host on the ITPro Podcast, where he was often found ranting about his love of strange gadgets, his disdain for Windows Mobile, and everything in between.
You can find Adam tweeting about enterprise technology (or more often bad jokes) @AdamShepherUK.





