How to make your email hack-proof
How to secure your inbox, enhance your mail and unlock secret codes

Even with the rise of social networks and messaging apps, email is still the most popular means of online communications and remains essential for registering with websites, confirming your identity and receiving important information.
Most email services are far from perfect, however, despite the introduction of GDPR and improvements to spam filtering and anti-phishing protection. Some of the most well-known services fail to protect your data from hackers, invade your privacy by scanning message content, and generally lack important features we all want and need.
In this advanced guide, we show you how to become an email power user by unlocking the full potential of your webmail service.
Create a fake 'burner' email address
When you use your real email address to register with a website, you're not only opening yourself to a deluge of marketing messages (despite the recent introduction of GDPR), you're also handing over an essential piece of personal information.
If the site suffers a security breach, your email address could fall into the hands of cyber criminals, compromising the safety of your other online accounts.
The best way to avoid being spammed, scammed and hacked is to create a temporary fake address using a disposable-emails service. Use this fake address to sign up to a website, click the link in the confirmation message that arrives in your alternative inbox and you'll gain access to the site without sacrificing your privacy or security.
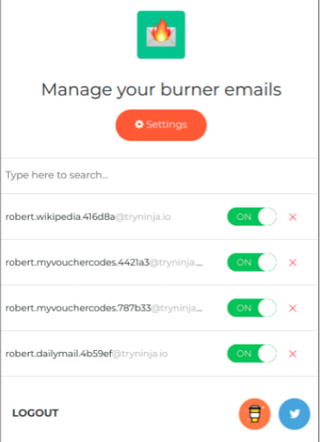
Burner Emails conceals your real email address when you register with sites
Get the ITPro. daily newsletter
Receive our latest news, industry updates, featured resources and more. Sign up today to receive our FREE report on AI cyber crime & security - newly updated for 2024.
Our favourite new tool for this task is Burner Emails. It's available for Firefox and Chrome, and also works with Opera and Vivaldi. This browser extension automatically detects email fields on web pages and lets you click them to generate and enter fake addresses. Messages sent to these addresses are then forwarded to your real account, so you won't miss important verification and confirmation emails. You can then delete or disable each 'burner' address so you won't receive any further communication from that site.
We also like the Firefox add-on Bloody Vikings, which lets you create fake addresses on the fly using 14 disposable email services, including Dropmail, Fake Mail Generator and Mailinator. Usefully it opens your temporary inbox in a background tab, so you can confirm your registration without leaving the page. Another handy Chrome extension is Disposable Temporary Email Address, which generates accounts that expire after 10 minutes.
Stop third-party tools reading your emails
Google recently admitted that the contents of Gmail messages are not only processed by computer algorithms but can sometimes be read by human third parties, when certain apps are granted access to user accounts. With so many useful tools available for Gmail, this situation is difficult to avoid, but it still pays to know exactly which apps you've allowed to access your emails so you can block any that look suspicious.
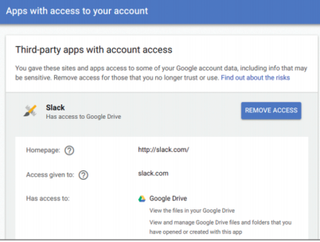
Remove unwanted third-party apps that have access to your Gmail account
To find out which of your apps can access your email, go to your Google Account and click the 'Apps with account access' link in the 'Sign-in & Security' section. Click Manage Apps to view further details about what personal data third-party apps can access, and click remove Access to disconnect undesirable tools from your Gmail account.
Make two-factor authentication easier to use
Two-factor authentication (2FA) also known as two-step verification adds a second layer of protection to your email account by asking you to enter a code when you sign in from a new device or if you've been logged in on your current one for 30 days. In January, Google software engineer Grzegorz Milka admitted that fewer than 10% of Gmail users have enabled this feature but if you're security-conscious, it's definitely worth setting up.
To do so, head here, click 'Get Started', then sign into your Gmail account and click 'Start Setup'. Enter your mobile number, choose how you want to receive the verification code and click Send Code. When you receive the six-digit code, enter it in the box and click Verify to add your phone number to your account.
If you prefer, you can use Google's Prompt feature, which saves you having to type a code each time. Instead, you tap Yes to confirm that you're trying to sign in from another device. This method is less secure, so Google recommends it's used only on phones and tablets that have screen lock activated. You can also print one-off back up codes to use as your convenience.
To set up 2FA for Outlook.co, go to the new 'Security Settings' page and sign into your account. Under 'Two-step verification', choose 'Set up two-step verification' to turn the feature on, then follow the instructions. You can opt to receive your verification codes by text message or phone call, or have them sent to an alternative email address, but the easiest method is to use an authenticator app, such as Microsoft Authenticator or Authy, which also works with Gmail.




