Ransomware that uses a fake children's charity for phishing
CryptoMix uses information lifted from children's charities to coerce victims into ransom payments
A new strain of ransomware has surfaced that pretends to be working for the good of a children's charity rather than for criminal gain, in an attempt to make handing over cash more palatable for a victim.
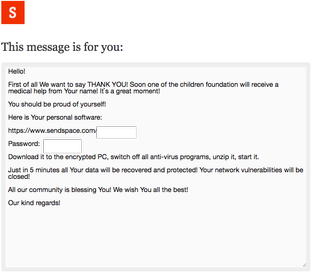
The newly discovered CryptoMix has been found masquerading as a Robin Hood-style of ransomware, providing links to a fictitious charity and an offer to put their name with their donation.
First spotted by cyber security firm Covewave, the ransom notes go so far as to include the names, diagnosis, and even pictures of young children that the ransom payments claim to support which, according to Covewave, the information appears to have been lifted from crowdfunding websites.
"In recent cases, Coveware observed ransom notes and communications that referenced a fictitious charity but real children," the company said. "The ransom communications begin with a .txt file that provides email addresses that the victim may use to contact the ransomware distributor."
Covewave have an example of the email exchange hackers use with this scheme. In the correspondence, they claim to work for a fictitious charity and give a description of a child's diagnosis and the funding amount being raised.
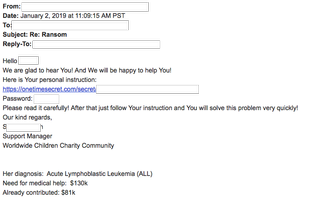
Email of a hacker using CryptoMix - courtesy of Covewave
Disturbingly, the email contained an image of what Croewave said appeared to be a 3-year-old girl lifted off a crowdfunding site.
Get the ITPro. daily newsletter
Receive our latest news, industry updates, featured resources and more. Sign up today to receive our FREE report on AI cyber crime & security - newly updated for 2024.
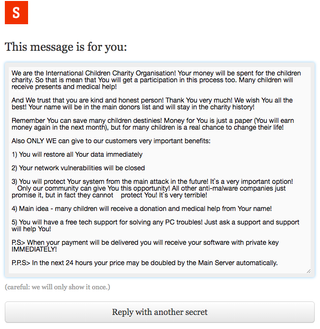
From there, the hacker will direct the victim to view payment information with instructions on a temporary page. This page includes bitcoin wallet payment instructions and more detail on the fake charity.
"We are guessing this tactic is meant to assuage the moral hazard associated with paying a ransom," Covewave explained. "It goes without saying that these cyber criminals did think this through. It is poignantly obvious that the charity is fake, and that the details of the child's case are lifted from other sites."
After paying the ransom, a victim is given more detail about the charity as well as a message suggesting their own name will be used alongside their donation.
CryptoMix has also been identified by Avast as a particularly nasty type of ransomware that can ultimately leaves your files locked even if you pay the ransom.
This strain of ransomware was first spotted in March 2016. The spread of this ransomware could be described as a medium level of prevalence and uses exploit kits as its main delivery method.
"Once CryptoMix infects a machine, it tries to communicate with its command and control server to establish a key to encrypt files. However, if the server is not available or if there is a connection issue, such as a blocked communication by a firewall, the ransomware will encrypt files with one of its fixed keys, or 'offline key'," it said.
Bobby Hellard is ITPro's Reviews Editor and has worked on CloudPro and ChannelPro since 2018. In his time at ITPro, Bobby has covered stories for all the major technology companies, such as Apple, Microsoft, Amazon and Facebook, and regularly attends industry-leading events such as AWS Re:Invent and Google Cloud Next.
Bobby mainly covers hardware reviews, but you will also recognize him as the face of many of our video reviews of laptops and smartphones.





