IT Pro Verdict
Pros
- +
Easy deployment options
- +
Good range of policies
- +
Helpful anti-spam features
Cons
- -
Basic reporting
If you’re after a cloud-managed endpoint protection solution that’s simple to deploy and administer, Avast’s business offering could be perfect. It comes in three flavours: we tested the top-dog Business Antivirus Pro Plus version, which supplements Avast’s core set of security features with a heap of extras such as Exchange and SharePoint protection, a data shredder, identity protection and even a webcam shield.
There are plenty of installation options. As usual, the Windows and macOS agents can be downloaded from the web portal and installed from a central distribution point, or you can email the installation link to your staff. Automated deployment is also possible by creating a master agent, scanning your Active Directory server and automatically pushing the agent to selected devices. By default, all key features are enabled on each endpoint, but you can create multiple endpoint groups, with policies determining which components will be active on which client.
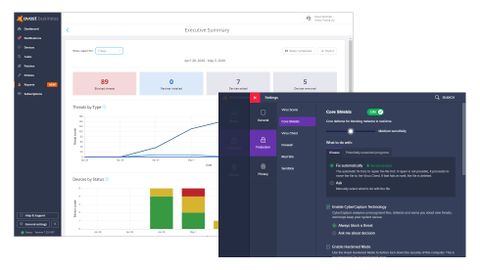
The management portal presents all of the most important information. The bar along the top provides a handy colour-coded readout of devices that are safe, vulnerable or in danger, and clicking on any of them instantly takes you to a filtered devices page for more information. We were highly impressed by how responsive this is: when a malware sample was blocked, a warning appeared on the dashboard within 30 seconds and an email alert dispatched at the same time.
Avast Business Patch Management review: Don’t give up the day job just yet Keep yourself protected with our list of the best security suites Avast Free Antivirus review: Pushy but protective
Below this, an alert status window provides a more detailed view of where threats have been discovered, with active links to the main device view page. A graph provides a broad overview of your Windows desktop, server and macOS devices, while another alongside provides a running tally of detected threats, again with links to the affected devices.

There’s a good range of policies that can be configured to customise your protection. File, app behaviour, mail and web shields can be applied to Windows workstations, along with a client firewall, anti-spam, browser security extensions and a sandbox for running virtualised web browser sessions and other apps. Windows servers enjoy additional policy options for Exchange and SharePoint protection, although macOS users get a raw deal as they only receive the file, mail and web shields. As well as configuring the agent’s behaviour, you can decide whether users should be allowed to access the interface themselves. If you permit this, they can check their own protection status, run scans, test unknown apps in the sandbox and use the webcam shield to keep video snoopers at bay.
One component that’s worth highlighting is the anti-spam module. We found this successfully tagged all our unwanted messages as spam or phishing emails, but it’s important to understand that tagged messages are still delivered to their recipients: you may want to configure your users’ mail clients to automatically delete tagged messages, or move them to the junk folder. Note too that the module runs on the workstation and that the web console doesn’t provide central anti-spam reports.
You can add another level of email protection using the Exchange server module, which scans mail at the transport level. This worked well for us, but be aware that enabling this policy automatically disables both the agent’s standard mail and web shields so that they don’t interfere with the scanning processes.
General reporting is pretty basic: Avast offers four standard report types, providing executive summaries, threats, devices and tasks, but there’s no option to create custom ones. There are also no mobile device management features – and unlike some of the competition, Avast only offers patch management as an expensive (and rather poor) add-on. Even so, there’s more than enough protection here to suit most SMBs and easy deployment is a plus point too.
Dave is an IT consultant and freelance journalist specialising in hands-on reviews of computer networking products covering all market sectors from small businesses to enterprises. Founder of Binary Testing Ltd – the UK’s premier independent network testing laboratory - Dave has over 45 years of experience in the IT industry.
Dave has produced many thousands of in-depth business networking product reviews from his lab which have been reproduced globally. Writing for ITPro and its sister title, PC Pro, he covers all areas of business IT infrastructure, including servers, storage, network security, data protection, cloud, infrastructure and services.