Sophos Central Endpoint Protection review: Because you’re worth it
It’s a tad pricey, but Sophos offers versatile user-based protection and the best mobile security around

-
+
Comprehensive management console
-
+
Smart deployment
-
-
Somewhat expensive

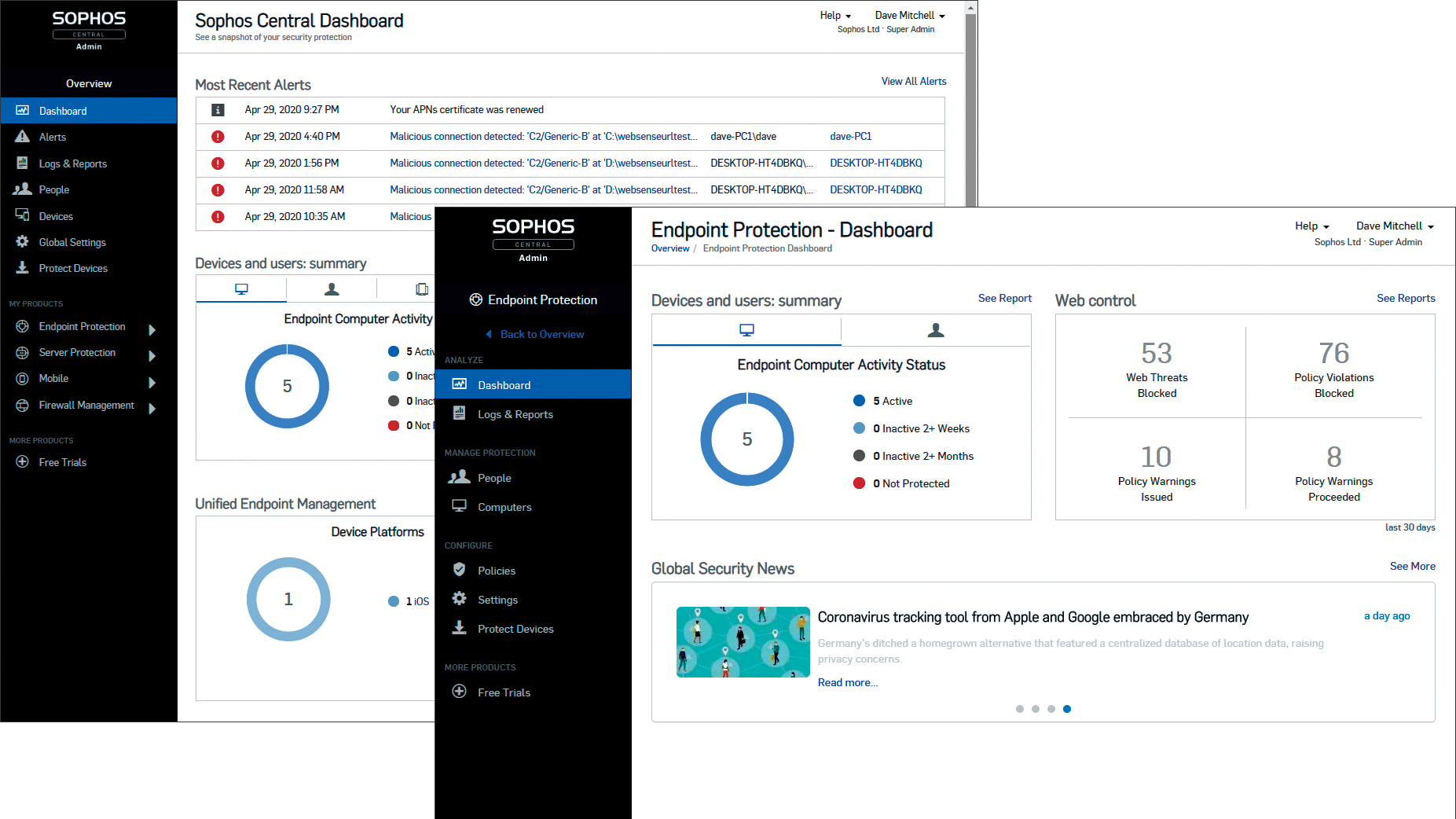
Sophos was one of the first security specialists to embrace cloud-managed endpoint protection, and over the years its Central solution has evolved into something impressively sophisticated. The cloud portal works with more or less every security component Sophos has to offer, providing one-stop management for all workstations, servers and mobile devices.
It opens with a handy dashboard view showing the most recent alerts, a summary of devices and users, plus details of how your access controls are performing. A menu at the side provides swift access to individual protection components, and if you have a Sophos firewall it can also be managed from here.
The deployment process is clever too. You can download the agent from the portal and install it the old-fashioned way, which takes about ten minutes – but if your users are set up on Active Directory, you can use the Sophos AD Sync tool to import users and groups into the portal, then email installation links to everyone with just a few clicks. Active Directory integration then allows you to create security policies that follow users around, regardless of which device they’re logged into.
Protection starts as soon as the agent is installed, with a base security policy applied to everything. Real-time scanning and automatic cleanup are enabled (with live protection ensuring that the agent has the latest threat information from Sophos’ labs), and all internet traffic and downloads are monitored.
Web controls can be applied to selected users too. Four predefined URL-filtering policies are supplied, but it’s easy to tweak these or create new policies of your own. These can include web restrictions, blocking adverts and risky downloads and blacklisting specific URLs, IP address ranges and site categories.
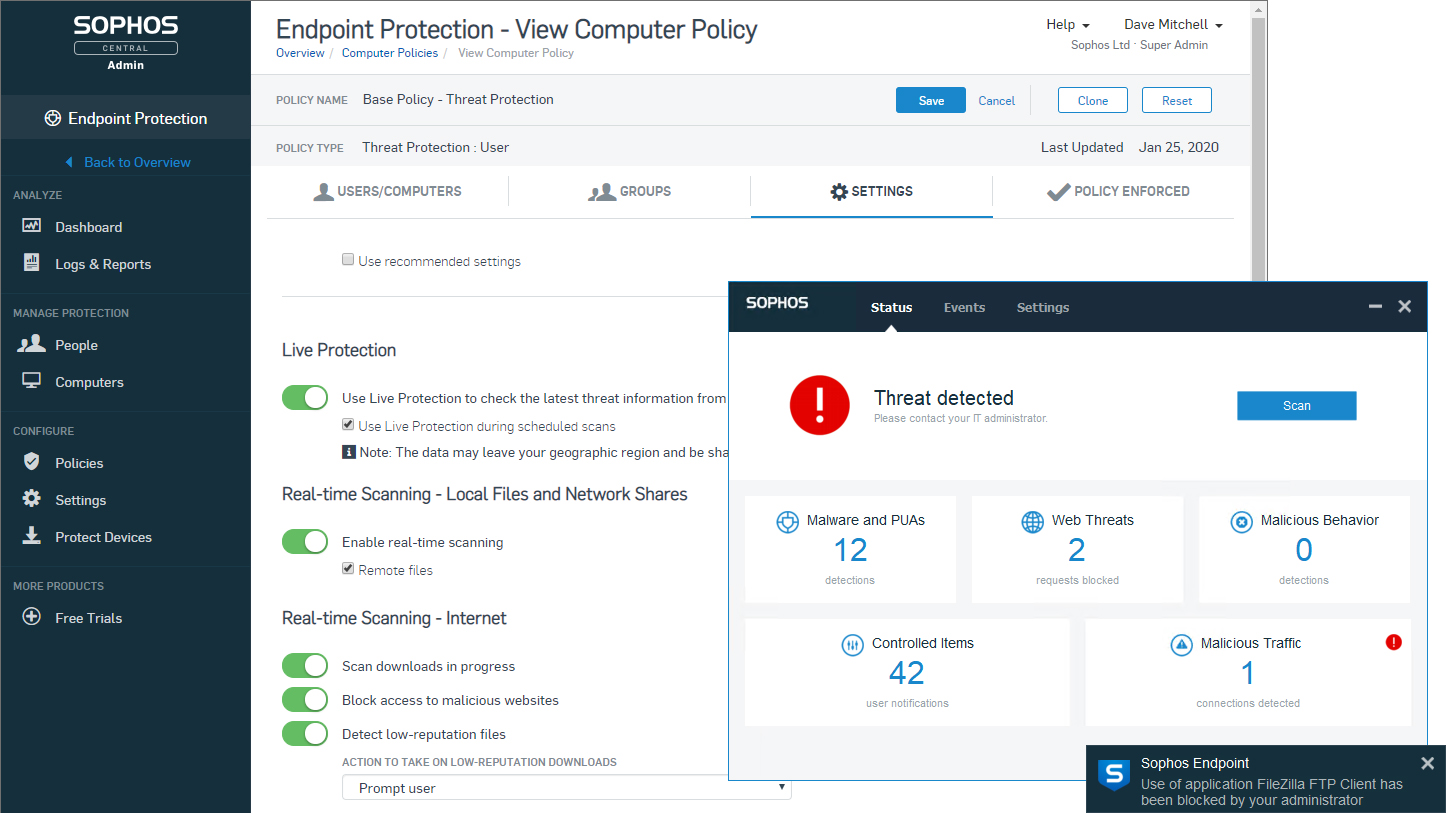
Application usage is controlled in much the same way. Sophos provides a list of over 1,000 apps to choose from, in categories ranging from browser plugins and email clients to encryption tools and FTP clients. You can completely block access to particular applications or merely monitor and log their use.
Another noteworthy feature of the software is its data-loss prevention option, which prevents users from transferring files containing sensitive data, such as bank account details or personally identifiable information. We tested this by trying to email a spreadsheet containing personal email addresses outside of the organisation and found that the Sophos agent wouldn’t even let us attach the file.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
The one area where Sophos proved a little erratic was alerting. During our tests we found that warnings about web-policy violations could take up to 50 minutes to appear in the portal dashboard and reports. The most important messages get through quickly, though: when we dropped our malware samples onto our test workstations, high-priority alerts appeared in the portal in one minute flat, with email warnings flying in shortly afterwards.
It’s also worth highlighting that the standard licence only covers workstations. If you want server protection, that’s an optional extra, starting at £69 per server per year. This works in just the same way as the desktop version, with the agent detecting the OS when it installs and configuring itself as needed.
Mobile coverage is another optional extra, but one that’s well worth considering, as the device management controls are stunningly good. Once we’d set up an APN, we were able to control virtually every feature and app on our iPads with remote locate, lock and wipe services all available.
No doubt about it, Sophos Central Endpoint Protection isn’t the cheapest option, especially if you’re looking to protect your entire hardware stack. Even so, its excellent protection features, user-centric policies and well-designed cloud portal make it a very appealing solution.
Dave is an IT consultant and freelance journalist specialising in hands-on reviews of computer networking products covering all market sectors from small businesses to enterprises. Founder of Binary Testing Ltd – the UK’s premier independent network testing laboratory - Dave has over 45 years of experience in the IT industry.
Dave has produced many thousands of in-depth business networking product reviews from his lab which have been reproduced globally. Writing for ITPro and its sister title, PC Pro, he covers all areas of business IT infrastructure, including servers, storage, network security, data protection, cloud, infrastructure and services.
-
 OpenAI just signed a bumper $38bn cloud contract with AWS – is it finally preparing to cast aside Microsoft?
OpenAI just signed a bumper $38bn cloud contract with AWS – is it finally preparing to cast aside Microsoft?News The move by OpenAI doesn’t signal an end to its long-running ties with Microsoft
By Nicole Kobie Published
-
 Colt DCS to expand West London data center campus in £2.5bn investment
Colt DCS to expand West London data center campus in £2.5bn investmentNews Three new hyperscale data centers and an innovation hub will be added to the site
By Ross Kelly Published
-
 Microsoft and Nvidia are teaming up again to support UK startups
Microsoft and Nvidia are teaming up again to support UK startupsNews Agentic Launchpad will offer participants AI expertise, training and networking, and marketing support
By Emma Woollacott Published
