Who do you think you are?
Most companies need to track access and resource use for security and accounting

There are many legitimate reasons for wanting to know where people are within a company building, and wanting to be able to allocate resources, such as the use of computers and printers, to particular people or departments. Security and accountability are governed by authentication, the ability to identify a person or device and prove his or her legitimacy.
Over the years, authentication methods have progressed from numbers and words, through artefacts, to measurement of biometrics and direct connection between a personalised gadget and the resource requiring access. Different techniques are needed for different levels of access, of course, and new methods are entering the field all the time.
PINs and passwords
The most widely used form of authentication is the Personal Identity Number, or PIN. Almost everybody requires a PIN to use an ATM and many people use them at work, to gain access to a building or to secure rooms within a building. PINs are often used in conjunction with pass cards, so the access system requires both the number and the magnetic strip or chip in a card to prove identity.
Passwords are more common than PINs on the Internet, but serve the same purpose, this time usually combined with a username or email address to provide a dual-source authentication.

If you're a regular Internet shopper, you'll probably need a notebook or encrypted repository for all the passwords required by the shops you visit. Secure passwords should involve numbers and punctuation characters, as well as upper and lower case letters, so the temptation is to use the same password in more than one place. That's not good practice.
The main problem with using PINs or passwords in business or in public places is that they can be revealed by somebody simply watching what's entered at an ATM or access point. To overcome this, passwords and PINs need changing regularly, but in a company there's then the problem of informing the entire workforce of each change.
Pass cards and tokens
An easier solution is to build the necessary security into the magnetic strip or embedded chip in a card. This can double as an identity card, with a picture of its owner and other info printed on its face. Swiping or touching the card on a reader then grants access to all the places and resources to which its owner is entitled.
The obvious disadvantage of the pass card is that the card itself can be lost or stolen, potentially allowing access to the wrong people. If the authentication method is attached to an object, rather than a person, there's always the possibility of misuse.
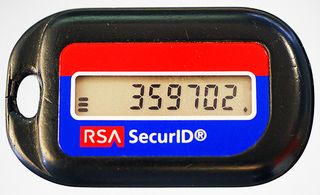
An extension of the hardware-based authentication is the RSA token. Here the person requiring authentication carries a badge or keyfob which displays a series of PINs either continuously or on demand. The person supplies a personal identification number and the number showing at that time on their RSA token, each time they need to gain access.
The combination of the two codes is unique but predictable, and to be misused a miscreant would need to know the person's own code, as well as having their physical RSA token to hand.
Biometrics
Still easier for the person needing authentication is to use a unique physical attribute: fingerprints and retinal scans are the most common forms of biometric security. Fingerprint scanners are now seen on laptops and smartphones, in place of password systems and don't suffer from the problems of a poor memory or somebody looking over your shoulder.

Retinal scans have so far been seen more in fixed locations, such as airports, but Samsung is rumoured to be working on a scanner which will use retinal scans to identify the owner of future smartphones. The advantage of a retinal scanner is that simply looking at the phone will unlock it easier than a finger or thumb scanner, let alone a PIN.
For more general use, face recognition that can be used with CCTV images is a target for biometric companies that has still to be realised. Recognition rates are currently too low to be used for higher security applications. It's still more accurate to get a human to compare a face with a photo than to get a computer to do it.
This restriction is true of voice recognition, too. Anybody who has used speech recognition for dictation will know that applications can still have trouble with speech from a voice with which they've been trained. Getting them to reliably recognise a voice from cold is an even harder task.
The Future
We're beginning to see Near Field Communication (NFC) technology being more widely deployed. This RF tag-based system has already been used to good effect in Oyster travel cards and contactless credit and debit cards, but it's now starting to be built into devices, too.
As well as being able to connect, say, a smartphone or tablet with a peripheral like a printer, NFC can be used to make payments in the same way as those contactless cards, by authenticating the bearer. The same proviso over having a gadget stolen applies, but with suitable authentication in the device itself, such as a fingerprint reader, it should be possible to make it secure.

Then there's the bottomprint seriously. Japan's Advanced Institute of Industrial Technology has designed a seat with 360 pressure sensors, which can recognise those who sit in it with 98 per cent accuracy. While this type of authentication won't be suitable everywhere, it could be used to good effect in car seats, identifying legitimate drivers and adjusting control positions, environment and even choice of music to suit.
It's even proposed that brain waves could be used for authentication. Taking an ElectroEncephaloGram (EEG) of somebody undergoing a particular thought activity and comparing that with the same thought at a later date could be used for identification. This is still in its very early stages, though and the mechanics of making this a convenient authentication method have some way to go.
There are numerous methods of proving somebody's identity, from simple numeric PINs through to thought experiments, and different techniques are suitable for different applications and levels of required security. All that said, it looks like user authentication will continue to become simpler, more accurate and more secure.
Find out how HP has implemented multiple user authentication layers in its LaserJet Enterprise Flow MFP device.
For more advice on transforming your business, visit HP BusinessNow
Get the ITPro. daily newsletter
Receive our latest news, industry updates, featured resources and more. Sign up today to receive our FREE report on AI cyber crime & security - newly updated for 2024.




