Keeping your documents secure
HP's multi-function printers put data security at the centre of their printing and scanning functionality.

In the world before digital communications technology became ubiquitous, documents were potentially more secure by their very nature. If a document was unique or limited in number, it would need to be physically stolen or copied in some way, which might involve laboriously photographing every page or, once the photocopier arrived, laboriously presenting each page to the photocopier window. But multi-function printers such as HP's LaserJet Enterprise Flow MFP M880z make it easy to switch documents between digital and physical realms, which potentially makes them easy to access for nefarious reasons as well as legitimate ones.
Fortunately, HP has taken this into account in the design of its multi-function printers, and put security at the heart of their design. This begins with device authentication, which can use Windows/Kerberos, LDAP or user PINs, designed to integrate with your existing infrastructure. HP FutureSmart provides role-based authentication and authorisation, so IT administrators can choose who has access to which features on the device. Fleet-wide policies can be applied with the HP Imaging and Printing Security Center, to help protect all HP devices used by the company.
FutureSmart also provides Encrypted PDF creation when scanning, where the user provides a password when scanning, which is used to create symmetric key encryption of the document. This employs built-in FIPS 140 validated cryptographic libraries from Microsoft. The Encrypted PDF functionality works alongside HP Universal Print Driver (UPD) Secure Encrypted Print, which will only allow you to print the document with the same password. The document remains encrypted across the entire workflow, even if you send it to another device in an office somewhere else in the world.

Even without documents that have been scanned to an Encrypted PDF, HP's UPD can keep your documents secure when they are sent for printing. In theory, it would be possible to intercept and capture printing data sent across a network. But with HP UPD 5.3.1 or later, Secure Encrypted Print can be used for a print job, securing the data at source and keeping it encrypted until it reaches the printer. This uses 256-bit AES symmetric keys, which are generated from a user-created password via FIPS 140-validated cryptographic libraries from Microsoft.
There are other options to keep data secure as it travels across the network to and from the device. One option is IPsec, as used by Virtual Private Networks, which can encrypt data before it is sent to destinations that also support IPsec. Alternatively, the Internet Printing Protocol can be used with SSL/TLS encryption. Device management data can be encrypted, too, when it is travelling between the device and the HP Embedded Web Server, HP Web Jetadmin, and other management tools. This data can be protected using SNMPv3 and SSL/TLS, allowing IT managers to centrally monitor and control printers with complete security.
With the optional HP Access Control and HP Smartcard Solution, authentication can be linked to proximity cards or smartcards. The hardware integration pocket on the side of the M880z allows integration of the necessary security solutions, such as card and badge readers. Physical security measures extend to the device itself, with both the MFP and the HP High-Performance Secure Hard Disk inside it able to be secured by a locking mechanism requiring a key, to impede theft or tampering. The USB ports, network ports, and any other ports can be disabled to prevent unauthorised use, too.
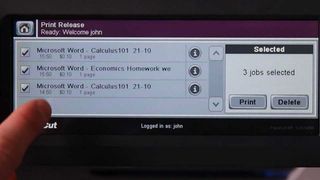
Documents can be held and released only to the person who submitted them. The HP Access Control Pull Printing function requires authentication at the device, and gives users the flexibility of pulling the documents from any device that is enabled with this feature. There's a manual memory lock, allowing incoming faxes to be saved until the intended recipient arrives with the appropriate PIN code. Anti-fraud features can be embedded into documents as they are printed, which will be invaluable for sensitive documents like prescriptions, birth certificates, or transcripts. Anti-fraud features are embedded before they are routed to the MFP and printed on plain paper by using the HP and TROY Secure Document Printing option.
The HP High-Performance Secure Hard Disk is a central feature for device security, ensuring that any data sent to the device for printing, or scanned with the device, remains protected. Data stored on the Hard Disk is encrypted, and sensitive data is securely overwritten when removed, using multiple mechanisms, including some that conform to U.S. National Institute of Science and Technology (NIST) Special Publication 800-88. Stored passwords are encrypted, too, so this potential chink in the armour remains firm. All jobs remain in an encrypted state until the relevant user accesses the device and allows the job to output.
One of the biggest changes to the modern business is the proliferating use of mobile devices, and HP has its eye on security here as well. Both HP wireless direct and touch-to-print use a secure peer-to-peer connection, allowing users to print without accessing your corporate network. Print files are encrypted, and with a configurable passphrase, you don't have to worry about who is connecting to your office printers. Security and user access settings can be easily set up with HP Web Jetadmin or the Embedded Web Server.
HP's multi-function printers provide a host of useful networked printing and scanning abilities, which can revolution the way your business handles its paper and digital documents. But this also means your data will be travelling across networks with even greater frequency. With certain documents being highly sensitive, even within the same company, knowing that firm authentication policies backed by solid data encryption are in place means that this revolution can be enjoyed with total confidence that your data will remain secure.
For more advice on transforming your business, visit HP BusinessNow
Get the ITPro. daily newsletter
Receive our latest news, industry updates, featured resources and more. Sign up today to receive our FREE report on AI cyber crime & security - newly updated for 2024.
Dr James Morris has worked as a technology journalist for over 25 years, including spending nine years on the staff of market-leading computer magazine PC Pro, the last five of which were as the publication’s editor. He specialises in enterprise-grade software and hardware, with a particular focus on content creation. He launched a pioneering video channel for HEXUS.net in 2006 and ran the video reviews channel for TrustedReviews.com for four years. He also runs a successful online digital content and commercial video production company, t-zero communications Ltd.
Dr Morris is a prolific technology writer and contributes commercial content for major IT brands including AMD, BlackBerry, Dell, Cognizant, HP, and IBM. He published a book on artificial intelligence, Can Computers Create Art? in 2009. He is also an academic, and is currently Pathway Director of the MA, Interactive Journalism at City, University of London.
Previously, he was course leader for the BA in Web Media Production at Ravensbourne University. He has a PhD in Philosophy, Art and Social Thought from the European Graduate School in Switzerland, a Master's in Media Arts from the New School in New York, USA, and a Bachelor's in Social Anthropology from the London School of Economics.
Dr. Morris can be found on Twitter at @Cyberwest, or emailed at j@tzero.co.uk





