IBM: Ransomware incidents "exploded" in June
IBM Security X-Force report also finds that ransom demands are increasing to as much as $40 million

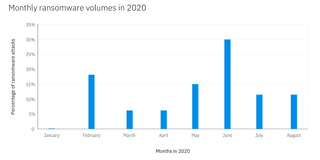
IBM says ransomware incidents "exploded" in June 2020, which saw twice as many ransomware attacks as the month prior.
The month of June accounted for one-third of all the ransomware attacks dealt with by IBM Security X-Force Incident Response this year so far, according to new findings published this week.
According to the report, one in four cyber security incidents in 2020 so far had been caused by ransomware, and IBM warns that ransom demands are also rapidly increasing, with some demands surpassing $40 million (£31 million).
Out of all ransomware attacks IBM observed, 29% were made up of the Sodinokibi (also known as REvil) ransomware-as-a-service (RaaS) attack model, which previously targeted entertainment and media law firm Grubman Shire Meiselas and Sacks.

In May, attackers claimed to have used the ransomware strain to compromise 756GB of data including contracts and personal emails belonging to high-profile celebrities such as Madonna, Lady Gaga and Bruce Springsteen.
Sodinokibi was also used in the January attack on foreign exchange company Travelex, which was kept offline for weeks and reportedly cost the firm £25 million.
IBM Security X-Force found that Sodinokibi had managed to attack over 140 organisations since its emergence in April 2019, most often targeting industries such as the wholesale sector (19%), manufacturing (18%) and professional services (16%).
Get the ITPro. daily newsletter
Receive our latest news, industry updates, featured resources and more. Sign up today to receive our FREE report on AI cyber crime & security - newly updated for 2024.
Three in five of the targeted organisations were based in the US, followed by the UK, Australia, and Canada.
According to the findings, over 36% of Sodinokibi victims decided to pay the ransom, and 12% of victims had their sensitive data sold in an auction on the dark web for prices ranging from $5,000 to more than $20 million.
IBM Security X-Force also managed to identify which cyber crime threat group is behind the elusive malware.
In a blog post detailing the findings, X-Force IRIS global security intelligence analyst Camille Singleton said that the team found “evidence suggesting that ITG14 — which shares campaign overlap with FIN7 — is at least one affiliate group connected to these attacks”.
“After investigating a Carbanak backdoor associated with a Sodinokibi ransomware attack, we discovered this Carbanak sample was similar to new Carbanak 64-bit variants, which have been connected to ITG14 tools and techniques. We also assess this sample is used exclusively by the group. This leads us to conclude that ITG14 is at least one affiliate group that contracts with Sodinokibi RaaS providers to deliver these attacks,” she explained.
IBM recommendeds that, in order to mitigate the risks of ransomware, companies should establish and maintain offline file backups, implement a strategy to prevent unauthorized data theft, employ multi-factor authentication and user behavior analytics, and conduct penetration testing to identify vulnerabilities.
Having only graduated from City University in 2019, Sabina has already demonstrated her abilities as a keen writer and effective journalist. Currently a content writer for Drapers, Sabina spent a number of years writing for ITPro, specialising in networking and telecommunications, as well as charting the efforts of technology companies to improve their inclusion and diversity strategies, a topic close to her heart.
Sabina has also held a number of editorial roles at Harper's Bazaar, Cube Collective, and HighClouds.





