IT Pro Verdict
Pros
- +
Includes tons of cyber security features
- +
Slick, customisable cloud-based management
- +
Strong VM support
Cons
- -
Client software has to be manually deployed
Acronis takes a broad view to data protection: its Cyber Protect software doesn’t just take care of backup, but adds a heap of AI-driven cybersecurity measures, including malware protection, vulnerability assessments, patch management, hard disk health monitoring and remote desktop services.
Both local and cloud management options are provided; we went for the latter, as it gives you the ability to extend protection to home workers. There are also Essentials, Standard and Advanced editions, with the top-tier package including shared protection plans, deduplication, backup fingerprinting and backup malware scans. Check out Acronis’ website for a full breakdown of the differences between the various versions.
Whichever permutation you opt for, all versions are subscription only. The Advanced licence includes protection for one physical or virtual server and 250GB of cloud storage for £458 per year; further 1TB chunks are £379 per year, while cloud seeding incurs a one-time fee of £59.
As for self-hosted backups, there’s plenty of flexibility. Supported destinations include SMB and NFS shares, IP SANs and tape drives, and Acronis also offers its own storage node service with deduplication.
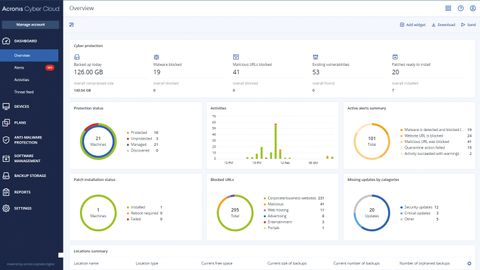
For management, the web-based dashboard offers a wealth of information about your protected systems and backup repository status, along with details of any malware detections, blocked URLs, missing patches and more. It’s customisable too, allowing you to personalise and reorganise widgets to focus on whatever’s most important to you.
The only clunky aspect of the cloud-based approach is agent deployment; the client software has to be downloaded from the portal and manually installed, which might not be ideal for full-time home workers. It’s not complicated, though, and you can check the Devices page in the console to confirm that all computers have been successfully registered.
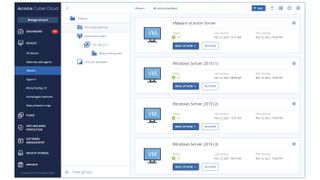
There’s also an agent specifically for Hyper-V systems, while for VMware you can download an agent VM and configure it with your cloud credentials and vCenter server details. Once we’d deployed these agents, the portal happily presented a list of all their VMs available for backup.
Cloud storage is automatically assigned to your account, and for local backups we were easily able to point the software to shares on remote Synology and Qnap NAS appliances using their UNC paths.
The specifics of your backups are configured in the form of plans, which define items to be copied, security settings, schedules and storage devices. A plan can be associated with any number of devices; a clever data protection map exposes files not covered by a backup plan, while plans created at the virtual host level will helpfully take in any new VMs as they’re added. Configuring hybrid backups is as easy as specifying two destinations in your plan, so each run backs up to both on-premises storage and the cloud repository. Malware scanning can be included in your plan too, along with URL filtering (using a predefined list of 44 categories), vulnerability assessments and other security checks.
Realising the benefits of automated machine learning
How to overcome machine learning obstacles and start reaping the benefits
Acronis also shines when it’s time for recovery. Regular system backups can be easily mounted as virtual machines, so you can browse and pick out individual files or folders for restoration. Backed-up VMs can be restored to their original location, either as a new VM on the same host or to another location. It’s fast, too, which is great news for your RTOs: we restored an entire Windows Server 2019 VM back to our vSphere host in just 100 seconds.
Acronis Cyber Protect is a great all-round data protection solution, thanks to its smart combination of cybersecurity measures and cloud-managed backup. The portal is well designed too, making it easy to create and manage hybrid backup strategies, and the protection for virtualised environments is first class.
Dave is an IT consultant and freelance journalist specialising in hands-on reviews of computer networking products covering all market sectors from small businesses to enterprises. Founder of Binary Testing Ltd – the UK’s premier independent network testing laboratory - Dave has over 45 years of experience in the IT industry.
Dave has produced many thousands of in-depth business networking product reviews from his lab which have been reproduced globally. Writing for ITPro and its sister title, PC Pro, he covers all areas of business IT infrastructure, including servers, storage, network security, data protection, cloud, infrastructure and services.