QNAP warns of ransomware targeting internet-facing NAS products
The manufacturer has provided a guide to securing vulnerable products amid ongoing attacks

QNAP customers have been advised that cyber attackers are targeting its network-attached storage (NAS) products with ransomware and have been encouraged to secure their devices at the earliest opportunity.
Ransomware and brute-force cyber attacks have been "widely targeting" QNAP's internet-facing NAS products, according to the manufacturer which published a products security statement on Friday.
Best NAS drives 2023: Which network storage appliance is right for you? 12 wonderful uses for a NAS Can you put an SSD in a NAS?
NAS drives that are exposed to the internet without any protection are particularly vulnerable to the attacks and users are advised to revisit their security settings to ensure devices are adequately protected.
The scale of attacks is currently unclear and QNAP also didn't specify what strain of ransomware the attackers are using, or where the attackers are based. IT Pro has contacted QNAP for additional comment.
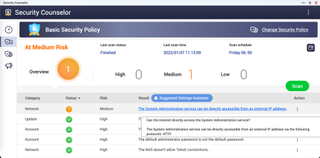
To check if a NAS drive is vulnerable to the attacks QNAP has observed, users should open the QNAP Security Counselor on their NAS products. The NAS is at high risk if there is an artefact that reads: 'The System Administration service can be directly accessible from an external IP address via the following protocols: HTTP' on the dashboard. QNAP also has a guide for users on how to check which ports on a router are exposed to the internet.
Securing the NAS
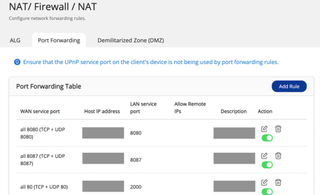
The first step to fully protect vulnerable products from the ongoing attacks is to disable the port forwarding function of the router. This can be completed via the management interface of a user's router. Users should check their settings and disable the port forwarding setting of NAS management service port which is set at port 8080 and 433 by default.
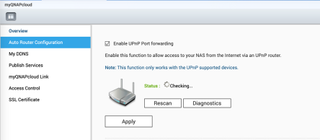
Users should finally disable the universal plug and play (UPnP) function of their QNAP NAS product in the QTS menu in myQNAPcloud. To do this, users can navigate to the 'Auto Route Configuration' tab in the QTS menu and unselect 'Enable UPnP Port forwarding'.
Get the ITPro. daily newsletter
Receive our latest news, industry updates, featured resources and more. Sign up today to receive our FREE report on AI cyber crime & security - newly updated for 2024.

Connor Jones has been at the forefront of global cyber security news coverage for the past few years, breaking developments on major stories such as LockBit’s ransomware attack on Royal Mail International, and many others. He has also made sporadic appearances on the ITPro Podcast discussing topics from home desk setups all the way to hacking systems using prosthetic limbs. He has a master’s degree in Magazine Journalism from the University of Sheffield, and has previously written for the likes of Red Bull Esports and UNILAD tech during his career that started in 2015.




