IT Pro Verdict
The 1100 Appliance combines tough gateway security with extreme ease of use. It runs the same software blades as Check Point’s enterprise products, is great value and can be upgraded without hassle if required.
Pros
- +
Simplified deployment; Good value; Software blades; Predefined security policies
Cons
- -
Anti-spam blade is over-enthusiastic
Focusing on SMBs and branch offices, Check Point's 1100 Appliance replaces the UTM-1 Edge. Check Point has added a range of features and simplified installation. The 1100 is also compatible with the firm's extended range of security software blades.
The family comprises three models all using the same fan-less desktop appliance with each licensed for different throughputs. The base 1120 model with Check Point's full NGTP (next generation threat prevention) package has a firewall throughput of 750Mb/sec and is recommended for up to 10 users.
An 1140 license pushes throughput to 1Gb/sec and is good for 25 users while an 1180 license opens it up to 1.5Gb/sec and 50 users. If you find your 1120 isn't up to the job you can buy a new license and upgrade it to a faster model in situ.
The 1100 Appliance is almost identical to the lower-cost 600 Appliance with one exception. The 600 models can only be managed using a web browser whereas the 1100 can be managed individually or centrally using Check Point's SmartCenter Server software.

The appliance has ten Gigabit ports and supports optional 11n wireless and an ADSL2+ modem
Options and installation
The appliance has eight Gigabit ports for LAN duties with two more for WAN and DMZ functions. Our review model had the optional b/g/n wireless AP enabled and you can order one with an ADSL2+ modem as well.
The base model costs around 365 and comes with the NGFW (Next Generation Firewall) software package. This provides an SPI firewall, IPsec VPNs, mobile access security, Check Point's Identity Awareness blade and the Advanced Networking and Clustering (ADNC) blade for ISP redundancy, as well as QoS and application load balancing.
The full NGTP license adds IPS, application controls, URL filtering, anti-virus and anti-spam. As an example, an 1180 Appliance with a one-year NGTP subscription costs around 1,156 ex VAT.
The appliance's browser interface provides a quick start wizard which steps through setting up an Internet connection and deciding whether to centrally manage the appliance or run it in standalone mode. The LAN ports can be configured as an eight-port switch or as individual ports each with their own security policies.
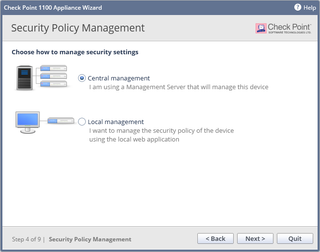
The 1100 Appliance can be managed centrally or in standalone mode via a web browser
Ready to go
A complete set of security policies is already active so the appliance starts protecting your network straight away. The Security Dashboard offers a status view of the software blades with quick links to their configuration and performance graphs.
There's no need to mess about with firewall rules as you can pick from Standard or Strict policies with a single click. The Access Policy tab allows you to modify basic firewall settings such as blocked services and you can add details of mail, DNS, FTP and Citrix servers you want protected.
Application filtering has a predefined policy blocking high security risks, torrents and other P2P apps. The URL filtering blade also has a pre-set policy which blocks inappropriate content such as gambling sites.
You can't change the base URL filtering policy but you can add other undesirable applications and extra categories to it. With two clicks you can also apply rate limits to bandwidth hungry apps and log all blocked traffic.
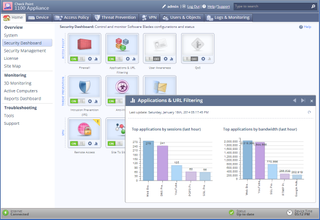
The appliance's web interface is well designed and provides easy access to all software blades
Blade configuration
The blades are simple to configure as most have few settings. Along with automatic signature updates, the AV blade can be set to scan inbound and outbound web traffic and has options to add file types and exceptions.
Extra URL categories can be added to the default security policy and Check Point provides an extensive list with eleven entries just for Facebook activities. Along with custom policies, the QoS blade can automatically prioritise traffic such as VoIP and ensure VPN traffic gets a set percentage of bandwidth.
The user awareness blade links user names to machines allowing security policies to be applied to user identities. VPN support is excellent as remote workers can connect using Check Point's mobile desktop client, SSL VPNs, LT2P or via a Remote app for iOS and Android.
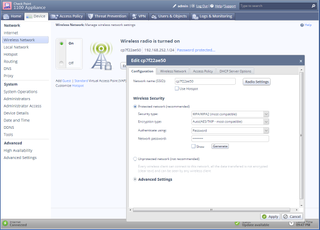
The optional wireless AP can be configured to provide guest access and secure wireless hotspots
Anti-spam and reporting
POP3 scanning is now included in the anti-spam blade and we tested this by leaving the appliance scanning live mail for two weeks and flagging the subject line of suspect messages. Detection rates were high as Check Point caught over 99 percent of spam.
False positive rates weren't so good, though, as of all the emails flagged by the appliance, 17 per cent were legitimate messages. As it's a managed service, you can't modify the spam scoring system and can set the blade to block the message or flag the email subject line or header.
The appliance can generate hourly, daily, weekly and monthly reports showing all network activity, top web categories, security threats and intrusion alerts. Each report also provides a bandwidth analysis and descriptions of events and application types but you can only print and not export them.
Conclusion
Check Point's 1100 Appliance offers a lot of classy network security features at an affordable price. It can be easily upgraded to keep in step with demand and the simple deployment and predefined security policies means it's virtually ready to go out of the box.
Verdict
The 1100 Appliance combines tough gateway security with extreme ease of use. It runs the same software blades as Check Point’s enterprise products, is great value and can be upgraded without hassle if required.
Chassis: Desktop
Memory: 512MB
Network: 10 x Gigabit (8 x LAN, WAN, DMZ) Ports: 2 x USB, RJ45 console
Other: SD Card slot, PCIExpress card slot Management: Web browser, SmartCenter Suite Power: External PSU
Options: 802.11 b/g/n wireless, ADLS2+ modem Warranty: 1yr NBD exchange
Dave is an IT consultant and freelance journalist specialising in hands-on reviews of computer networking products covering all market sectors from small businesses to enterprises. Founder of Binary Testing Ltd – the UK’s premier independent network testing laboratory - Dave has over 45 years of experience in the IT industry.
Dave has produced many thousands of in-depth business networking product reviews from his lab which have been reproduced globally. Writing for ITPro and its sister title, PC Pro, he covers all areas of business IT infrastructure, including servers, storage, network security, data protection, cloud, infrastructure and services.



