IT Pro Verdict
Pros
- +
Strong security focus
- +
Highly polished, easy-to-use interface
- +
Powerful range of integrated tools and features
Cons
- -
Backup scripts are a little sensitive
One of the most broadly cross-platform file-level backup solutions around, the Duplicati backup utility runs in your web browser via its own local web server on Windows, macOS and Linux. It’s nonetheless easy to install and use on any PC, with notification area shortcuts that make it easy to access its browser-based interface.
When you first install and configure Duplicati you’ll be asked whether your PC has multiple users and prompted to set a password to prevent others from accessing your backup data if that’s the case.
Duplicati is more overtly security-focused than many other backup tools. As well as prompting you to restrict access to them, AES-265 encryption is enabled by default for all the backups it creates, and you’re prompted to set a passphrase for each backup. It’ll also nag you if your passphrase is too weak or if you attempt to store data on a remote location without password protection.
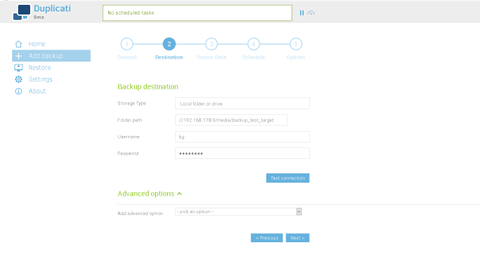
It supports a massive variety of backup destinations, including cloud-based options such as Amazon S3 buckets and Dropbox accounts, a variety of network locations and protocols, and local drives. That last category is surprisingly broad, as it not only includes connected USB devices but also, rather counter-intuitively, SMB/CIFS shares on your local network, as used by many NAS devices and file servers.
To use an SMB target, you have to enter the full folder path, including IP address and your username and password on the target device. Regardless of where your backup target is, you should give each backup job its own directory to avoid conflicts under Duplicati’s default settings.
Duplicati can back up any file or folder on your hard disk or other connected media. You can use filters to exclude specific content, as well as optionally excluding hidden, system and temporary files, or those over a specified size. Should you need to be able to back up open files using Volume Shadow Copy Services, you’ll have to enable the –snapshot-policy advanced option in your backup job and ensure that the Duplicati service or software has administrator privileges.
You’ll be prompted to set a backup schedule and can configure it to use a range of space-saving backup retention options. By default, everything is kept, but selected older backups can be automatically deleted as they age out of a specified time frame.
Duplicati is powerful and flexible, with advanced features including command line utilities and the ability to run pre- and post-backup scripts, but it’s also a little more sensitive than some of its rivals. With default settings in place, any error will halt the entire backup, which means that, if you’ve not got everything perfectly configured or if something significant changes in the file or folder structure that you’re backing up from or to, your backup routine will be interrupted.
It gives you plenty of warnings to tell you what’s happening, though, and you can override this by enabling the –allow-missing-source advanced option, which you’ll want to do for any backup job that includes removable media.
All restoration options are contained within the Duplicati web interface. You can browse and search through backups by date to find and restore specific files and folders to the location of your choice, or you can carry out a full-backup restoration, either to the original location or elsewhere.
Duplicati is our new favourite free backup tool. It’s under more active development than many of its rivals, but our tests found that, for a typical workstation, the current Duplicati 2.0 beta is a stable and refreshingly well-designed file-level backup and restoration tool with a wealth of very modern quality-of-life features.
Duplicati system requirements
| Windows 7/8/8.1/10//Server 2008-2016 |
| Linux |
| macOS |
| .NET 4.6.2+ or Mono 4.8.0+ |
K.G. is a journalist, technical writer, developer and software preservationist. Alongside the accumulated experience of over 20 years spent working with Linux and other free/libre/open source software, their areas of special interest include IT security, anti-malware and antivirus, VPNs, identity and password management, SaaS infrastructure and its alternatives.
You can get in touch with K.G. via email at reviews@kgorphanides.com.