Researchers warn of spear-phishing exploit in Google Docs
Hackers have found a way to use Google's comment function to dupe victims into clicking on malicious links

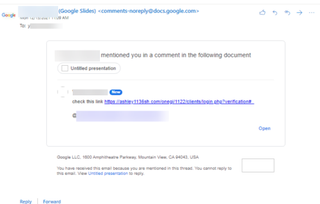
Threat actors have found an exploit in a Google Docs comment feature that uses Google's own automated email notification function to send malicious links.
Email security specialists Avanan said it had notified Google of the flaw on 3 January after noticing a spike in usage over December 2021.
The attack involves hackers using their own Google accounts to create a Google Doc, to which they simply invite a target using the comments section with the '@' function. This automatically sends a notification email to the intended target's inbox, informing them that another user has commented on a document and mentioned them. The email is from Google, and so it is difficult to tell whether the message is malicious.
However, the comment on the email can be loaded with a malicious link for phishing sites or malware, and there appears to be no filtering mechanisms in place, according to Avanan. What's more, the hackers email address isn't shown in the notification; the recipient will only see a name, making it very easy to impersonate a victim's colleagues or friends.
The exploit is very simple to execute and has been available since the Autumn of 2020. Google has attempted to mitigate the problem but are yet to fully close it off, partly due to the fact it requires its own email service to work.
Attackers also aren't required to share the document with their targets, as simply messaging them is enough to trigger the email alert. Avanan suggests that the same techniques work on Google Slides and other collaboration tools within the Google's Workspace suite.
Outlook users appear to be the favoured targets, according to Avanan, but it's believed the exploit has used over 100 Google accounts and has already attacked 500 inboxes across 30 different organisations.
Get the ITPro. daily newsletter
Receive our latest news, industry updates, featured resources and more. Sign up today to receive our FREE report on AI cyber crime & security - newly updated for 2024.
To protect yourself, and your organisation, Avanan recommends avoiding clicking on links in emails, deploying stricter file-sharing rules across Google Workspace, and using an Internet security service from a trusted vendor, particularly one that features phishing URL protection.
Bobby Hellard is ITPro's Reviews Editor and has worked on CloudPro and ChannelPro since 2018. In his time at ITPro, Bobby has covered stories for all the major technology companies, such as Apple, Microsoft, Amazon and Facebook, and regularly attends industry-leading events such as AWS Re:Invent and Google Cloud Next.
Bobby mainly covers hardware reviews, but you will also recognize him as the face of many of our video reviews of laptops and smartphones.





