Russian-linked spyware 'among most sophisticated ever discovered'
Monokle spyware boasts extensive list of potential hacking tools

A highly sophisticated strain of Android spyware has been discovered which is thought to be linked to a Russian defence contractor previously implicated in the interference of the US 2016 presidential elections.
Researchers from Lookout say the dangerous spyware, known as Monokle, can perform a range of hacking tasks, such as exfiltrating sensitive data, issuing remote access commands on devices, and launching man-in-the-middle attacks (MITM).
The spyware, which has been traced back to the Special Technology Centre (STC), a St. Petersberg-based company with a previously unknown history of developing apps, has been actively infecting users since 2016. Activity has been low in volume but consistent throughout the years, peaking in 2018.
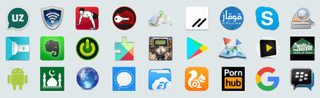
Monokle has so far operated as a trojan, embedding itself into popular apps such as Evernote, Wickr and Skype and then launching a varied list of attack types from a user's machine. It tricks users into downloading it by disguising itself as popular legitimate apps such as encrypted messaging services, productivity boosters and Android update services. It spoofs these apps logos and offers seemingly legitimate functionality.
It's believed that Monokle operates entirely on the Android operating system. While there is evidence of an iOS version in development, researchers said there have been no observed active infections on Apple's operating system to date.
If a user does find themselves infected with this intensely effective and capable strain of spyware, they will be prey to the array of malicious features. The spyware is said to be invisible to an infected device's Process Manager and, because of its remote access trojan (RAT) functionality, it's likely it would record most of your calls and background audio, and keep logs of texts, calls, passwords and pin codes.
Data exfiltration is also a big part of Monokle's functionality. It's said to have the ability to retrieve calendar information, including the date and time of an event, and the description of it. It can also collect account information from some of the most popular social media apps around, including Instagram, WhatsApp and Skype.
Get the ITPro. daily newsletter
Receive our latest news, industry updates, featured resources and more. Sign up today to receive our FREE report on AI cyber crime & security - newly updated for 2024.
In addition, Monokle can retrieve contacts, emails, call and browsing histories, accounts with corresponding passwords and track device location. It can also install attacker-specified certificates to the Android trusted-certificate store, which would allow it to conduct man-in-the-middle (MITM) attacks against TLS traffic.
Researchers were unable to access any of Monokle's exfiltrated data and can only speculate on the potential targets of the spyware, but possibilities listed include those interested in Isalm, interested in or associated with the Ahrar al-Sham militant group in Syria and those living in or associated the Caucasus regions of Eastern Europe - among others.
These guesses were made through inferred information such as the namings of Monokle-infected apps such as 'Ahrar Maps' and 'caucus'. Most apps were written in English but some were also in Russian and Arabic.
The researchers "found strong links that tie STC's Android software development operations to Monokle's indicators of compromise (IOCs) [and] shared command and control infrastructure used by both legitimate and malicious Android applications produced by STC," the report read.
"The Defender application and related software has been referred to by an STC developer as developed 'for a government customer,'" it added.
The report's findings have forced experts to once again raise awareness of the necessity of only downloading verified apps from legitimate sources.
"The Monokle malware mainly infects devices through corrupted versions of legitimate apps," said Paul Bischoff, privacy advocate, Comparitech.com. "For this reason, it's important for all Android users to get apps from a trusted source."
"Avoid downloading apps from third-party app stores and APK downloads," he added. "App developers don't publish their apps on these sites, so they're put there by unknown third parties. The apps from unreputable sources often look identical, but in fact, contain malware."

Connor Jones has been at the forefront of global cyber security news coverage for the past few years, breaking developments on major stories such as LockBit’s ransomware attack on Royal Mail International, and many others. He has also made sporadic appearances on the ITPro Podcast discussing topics from home desk setups all the way to hacking systems using prosthetic limbs. He has a master’s degree in Magazine Journalism from the University of Sheffield, and has previously written for the likes of Red Bull Esports and UNILAD tech during his career that started in 2015.




