The SSDs are preconfigured as three RAID5 arrays one for the Windows OS, another for the Commvault database and the third for the deduplication hash database. The standard hard disks are set up in a RAID5 array ready to be used as Commvault disk libraries.
Disk library arrays aren't assigned drive letters as Commvault uses mount paths to access them. Backup jobs secure data to selected mount paths and an advantage is they can be moved to other physical locations if required.
The Console provides a wizard which helps configure the CommCell environment along with storage, schedule and subclient policies. Help is also provided for deploying agents, protecting VMware and Hyper-V hosts and organising job monitoring and reporting.
Commvault's deduplication adheres to the common practise of breaking up data streams into chunks, computing hashes for each one and storing them in a database. Policy options available are MediaAgent-side for high speed LAN connections, source-side for data coming over low bandwidth WAN links and global deduplication.
Data restoration is easy and we had no problems recovering our SQL databases
The CommCell
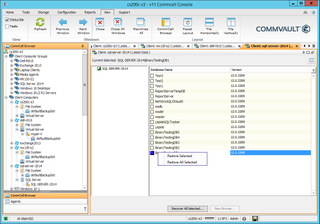
For testing, we deployed agents to our Windows Server 2012 R2 systems, Hyper-V hosts, Exchange 2013 and SQL Server 2014 servers plus Windows desktops. During this phase we loaded the virtualization agent package on our Hyper-V hosts, the SQL component on our database hosts and the Exchange database, mailbox and public folder components on our Exchange 2013 server.
Subclients are used to create logical groupings of content that you want protected. These range from specific drives, folders and files, share paths, databases and so on and can also include options for encryption and links to your deduplication policies.
Client computer groups apply common settings to multiple systems. Smart groups take this further as they use rules based on criteria such as installed agent packages to automatically add new and existing clients to the group.
Storage policies are even more powerful as these control the CommServe disaster recovery backup processes plus data protection and archiving functions. For the latter, we could choose from an extensive range of data retention rules, assign a deduplication policy and if not, select a disk library for the primary backups and enable encryption.
Conclusion
The Eternus CS200c S3 is a complete data protection and management solution presented in a classy hardware package. Pricewise, it's well suited to SMBs but its versatility also makes it good choice for remote office deployments where it can provide local protection plus replication to Fujitsu's enterprise CS800 or CS8000 appliances back at the head office.
The preinstalled Commvault software offers a stunning range of features and the simplified licensing make it very flexible. There's no denying it presents a steep learning curve to the uninitiated but once configured as required, it'll make data protection and recovery a breeze.
Verdict
A good choice for SMBs and mid-sized business that want the best data protection features money can buy and all presented in a classy hardware appliance
Chassis: 2U rack
CPU: 2 x 1.7GHz E5-2603 v4 Xeon
Memory: 32GB DDR4
Storage: 3 x 240GB Samsung SATA SSD, 5 x 1TB Seagate Constellation SATA HDD
RAID: Fujitsu PRAID EP420i 12Gbps SAS/2GB cache
Array support: RAID0, 1, 1E, 10, 5, 50, 6, 60
Network: 2 x 10GbE, 4 x Gigabit DynamicLOM card
Expansion: Fujitsu PSAS P400e SAS3 HBA
Power: 2 x 450W hot-plug PSUs
Management: Fujitsu iRMC S4 with Gigabit
Software: Windows Storage Server 2012 R2, Commvault v11
Warranty: 3 years on-site NBD
Dave is an IT consultant and freelance journalist specialising in hands-on reviews of computer networking products covering all market sectors from small businesses to enterprises. Founder of Binary Testing Ltd – the UK’s premier independent network testing laboratory - Dave has over 45 years of experience in the IT industry.
Dave has produced many thousands of in-depth business networking product reviews from his lab which have been reproduced globally. Writing for ITPro and its sister title, PC Pro, he covers all areas of business IT infrastructure, including servers, storage, network security, data protection, cloud, infrastructure and services.



