IT Pro Verdict
The e250’s hardware upgrade delivers superior UTM performance and combines this with a fine range of network security measures including wireless hotspot management
Pros
- +
Good value; Simple subscription pricing; Big boost to UTM performance; Integrated wireless security
Cons
- -
Annoyingly noisy cooling fans; Trusted network can’t be segmented
Although best known for its endpoint security software, Panda Security has always offered a solid range of business security appliances that have been nothing if not keenly priced. Unfortunately, performance has not been a strong point but the new GateDefender e250 aims to remedy this.
Taking over from the e9100lite, it claims to boost UTM throughput from the meagre 95Mbits/sec of its predecessor to a much more impressive 590MBits/sec. Even better, it does it at the same price as its predecessor.
It's easy to see how Panda has achieved this as the e9100lite only had an elderly 2.6GHz dual-core Pentium E5300 and just 2GB of DDR2 memory. The e250 has been beefed up with a quad-core 2GHz Intel Core i5-4590T alongside 4GB of DDR3 RAM.
As with the e9100lite, we found the cooling fans excessively noisy. With a tiny 35W TDP, the Core i5 processor is a cool customer so we can't see why it needs a massive heatsink and three fans all running as high as 8,000rpm.
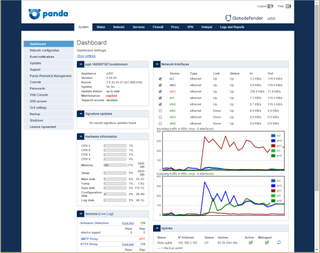
The web console dashboard shows all wired and wireless activity along with appliance utilisation
Security features
We like Panda's simplified licensing scheme as you pay a single yearly subscription for everything. Along with an SPI firewall and support for IPsec and SSL VPNs, the subscription activates anti-virus, IPS, anti-spam, web content filtering and application controls.
Internal hard disks are unusual at this price. The e250 uses mirrored 320GB SFF SATA drives to provide a spam quarantine area and web cache.
Another feature that adds even more value is built-in wireless network management and unlike many other vendors that offer this, the e250 will work with any access point (AP). You connect the AP or a switch carrying wireless traffic to any port on the appliance, apply security policies and create a wireless hotspot with login portal and billing scheme.
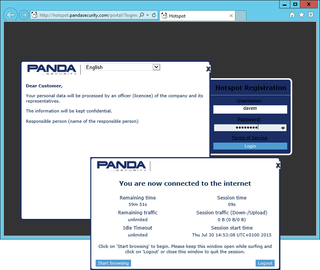
The e250 allowed us to set up wireless hotspots with billing schemes and Internet access restrictions
Colour by numbers
The e250 provides eight Gigabit Ethernet ports which can be assigned to LAN, WAN, DMZ or wireless network duties. A quick-start wizard made light work of installation as it guided us through configuring trusted and uplink ports and applied a base set of firewall security policies to provide immediate protection.
Panda employs colour codes for ports and uses green, red, orange and blue zones for trusted, Internet, DMZ and wireless services respectively. This helps when configuring the firewall as security policies can be swiftly applied by selecting the zone colours for source and destination networks.
WAN failover is available as we could define multiple ports as uplinks in the red zone and use static or DHCP addressing. Each extra uplink can be set so they are only activated if another specific uplink port goes down.
This colour zoning method does have limitations for defining different trusted network segments though. Essentially, you can only have a single trusted network subnet as the green zone is assigned one IP address and a DHCP server.
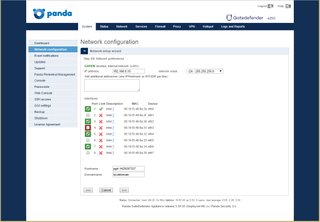
Ports are assigned colour-coded zones
Web filtering and anti-spam
The e250 provides proxies for controlling HTTP, HTTPS, SMTP, POP3 and FTP traffic. The HTTP proxy can be transparent or non-transparent and we used the former as this didn't require any changes made to our users' browser settings.
The HTTP proxy can have AV scanning applied. For web filtering, Panda provides five general URL categories covering themes such as productivity and security and within these are a total of 83 sub-categories. Proxy authentication can also be applied using the local appliance, Active Directory, LDAP or RADIUS.
The POP3 proxy uses the SpamAssassin service to scan inbound mail. We used it to tag the subject line of suspect messages but they can't be moved to the quarantine area.
Quarantining is available with the SMTP proxy which uses the CommTouch hosted service and requires details of your internal mail server. It provides spam checks plus virus scanning and will move suspect messages to the appliance's quarantine store.
Performance and reporting
For performance testing, we used the lab's Ixia Xcellon-Ultra NP load modules and IxLoad control software. The IxLoad software was configured for two client/server streams with requests for 1MB web page sizes.
With AV enabled in the HTTP proxy, we recorded a maximum steady throughput of 900Mbits/sec 35% lower than Panda's claimed 1.4Gbit/s. This was the best we could achieve as increasing the load further maxed out all four CPU cores at 100% causing traffic throughput to fluctuate wildly.
There were no such problems with the IPS service enabled. We recorded a steady throughput of 590Mbits/sec which is exactly what Panda's claims for full UTM performance.
On-board reporting tools are good as we could keep an eye on firewall activity, view graphs for proxies and services and check on traffic flows. MSPs can take advantage of Panda's Perimetral Management Console (PMC) which provides a central point of administration for all their Panda appliances with facilities for status monitoring and tools for remote firmware upgrades.
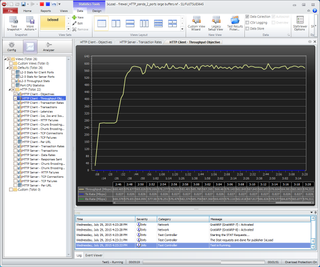
Our Ixia IxLoad test shows the e250 delivering a steady 590Mbits/sec UTM performance
Conclusions
The GateDefender e250 delivers a solid range of security measures and teams them up with some useful wireless hotspot management features. Its port-zoning feature isn't as versatile as that used by Watchguard's Firebox appliances but the e250 is still good value and just as easy to deploy.
Verdict
The e250’s hardware upgrade delivers superior UTM performance and combines this with a fine range of network security measures including wireless hotspot management
Chassis: 1U rack
CPU: 2GHz Intel Core i5-4590T
Memory: 4GB 1,600MHz DDR3
Storage: 2 x 320GB Hitachi SATA SFF mirrored hard disks
Network: 8 x Gigabit Ethernet (LAN, WAN, DMZ, Wireless)
Other ports: 4 x USB 2, RJ-45 serial, VGA
Power: Internal power supply
Management: Web browser, PMC
Dave is an IT consultant and freelance journalist specialising in hands-on reviews of computer networking products covering all market sectors from small businesses to enterprises. Founder of Binary Testing Ltd – the UK’s premier independent network testing laboratory - Dave has over 45 years of experience in the IT industry.
Dave has produced many thousands of in-depth business networking product reviews from his lab which have been reproduced globally. Writing for ITPro and its sister title, PC Pro, he covers all areas of business IT infrastructure, including servers, storage, network security, data protection, cloud, infrastructure and services.


