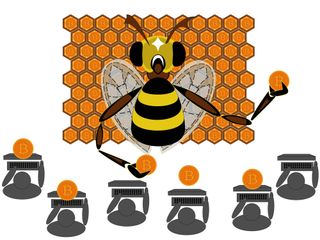
Is your browser secretly mining cryptocurrencies?
Your PC or smartphone could be being dragged down by secret Bitcoin mining software in apps and websites

Have you noticed your web browser swallowing more of your computer's resources recently? It's tempting to believe that Google Chrome's memory hogging is getting worse, but it could be that the site you're visiting is secretly harvesting your "spare" CPU cycles for a profit.
Amid a dramatic, volatile increase in the value of virtual currencies such as Bitcoin and Monero, mining them is an increasingly tempting source of income. So much so that a new set of JavaScript-based mining tools designed to help websites legitimately earn money from their visitors are being subverted to steal CPU cycles on the quiet.
"You're effectively stealing resources from someone else and trying to make money out of it," says Simon Edwards, security architect at Trend Micro. "The impact on users of affected devices are clear in increased device wear and tear, reduced battery life and comparably slower performance."
Cryptocurrency mining is big business, and with the cost of creating competitive specialist rigs escalating, a distributed model makes sense - provided the participants are aware that their processors are being used as mining tools.
What's yours is mined
CoinHive is a tool that allows web browsers to mine for cryptocurrencies in the background
However, in the few weeks since the technology for mining currency in browser windows has been released, researchers have seen a surge in abuse - both on websites and in Android apps.
Platforms such as CoinHive and JSECoin can be installed legitimately within web tools to, as JSEcoins puts it "carry out the mathematical hashing process in the background while browsing a website, using excess CPU power which would be otherwise wasted".
Get the ITPro. daily newsletter
Receive our latest news, industry updates, featured resources and more. Sign up today to receive our FREE report on AI cyber crime & security - newly updated for 2024.
JavaScript on the website runs in the end user's browser and goes through the process of mining the blocks. In return for running the code, websites receive 70% of the currency generated from users on their sites.
"Client-side mining on websites was not a thing until recently because JavaScript (Flash, or whatever) didn't have good performance for mining, and mining required downloading gigabytes of the blockchain, which is not possible for site visits that may only last a few seconds," says Denis Sinegubko, founder of Unmask Parasites and senior malware researcher at security firm Sucuri.
"That was until this autumn when JavaScript mining platforms emerged - they chose Monero coins, whose mining algorithm had comparable performance even on client computers."
Hackers have been quick to exploit the new tools. Security firm Trend Micro recently spotted two apps in Google Play Store, while security company Sucuri says it had seen at least a thousand cases of infected sites running WordPress plugins for CoinHive.
Pirates' plunder
The first widely publicised use of client-side CPUs for clandestine mining came with the news that ageing file-sharing site The Pirate Bay had been caught running the tools surreptitiously, after users spotted an increase in processor activity when visiting the site. The site had given no notice, nor offered any opt-out for the mining script.

Torrent site Pirate Bay was one of the first to deploy secret currency miners
It's more widespread on the murkier parts of the web, such as adult and file-sharing sites, where visitors are likely to dwell rather briefly dip in to read a news story.
Security experts say a simple declaration that they were using the tools would mean websites were acting responsibly and legitimise the technology, but many prefer to drop the mining code into browsers without warning. "Most sites will sneakily use this approach, embedding it into anything that can run JavaScript, says Bruno kvorc, founder of cryptocurrency site Bitfalls.com, which recently, and openly, deployed the technology in a trial. "It's easy to drop it on unsuspecting and technically illiterate users, because we're so used to browsers eating our RAM and CPU all the time."
Developers are also targeting apps delivered via Google Play, which embed the technology into web browsers within apps. "It all started about a month ago and currently there are dozens of CoinHive clones that use the same tactics - they set up a small hidden browser inside an app and use the very same ConHive code to do the mining," says Andrey Meshkov, CTO of advert blocking company AdGuard.
"Its profits are very low but the number of apps that are looking to use this is alarming and Google Play doesn't have any real process [for blocking this], so nothing stops them from embedding some kind of miner in there."
Opportunity to earn
Although the abuse risks ruining this nascent technology before most people have even heard of it, industry watchers believe that CPU mining could actually work as a web currency. With advertising revenue increasingly hard to come by due to the dominance of Google and the increased use of ad-blockers, mining could provide an alternative revenue stream.
"It could be positive, not just as a replacement for adverts," says Meshkov. "There are a lot of paywalls and wouldn't it be better not to pay for a subscription, but to mine for an hour and then get access. But the whole model could be destroyed by all the guys that use it unlawfully. If you can opt out and provide a choice this is fine, but when they do it in a hidden way then it's pure malware."
However, even legitimate sites will struggle to make much money from mining and some have swiftly dropped the technology because the return on investment simply wasn't worth the hassle. "We tried going that route (with a full up-front warning to people, and a permanent opt-out button right smack in the middle of the header), to spare our readers from having to see ads," says kvorc.
"At a meagre 8,000 visits per day on average, the payout was under $4 per month. That, coupled with the fact that many people's antivirus programs went crazy, and the fact that it's a huge battery drain on laptops and mobile devices, convinced us that it was in no way worth it."
What's the damage?
How much of a problem can the hidden miners be for end users? Well, if websites or apps don't throttle the CPU usage, the strain on hardware - and particularly battery life - can be dramatic.
"This was not sustainable for long periods of time," says Bitfalls.com's Bruno kvorc, who implemented an early version of the technology. "Someone reading a post for 10 minutes would have 5% of their battery eaten at 40% mining efficiency. "That's a lot, and most other sites didn't even stop at 40%, they went to 90%+. We used 20% and informed people in advance, and gave them the option to opt out."
"Those who heard about it from mainstream media were understandably scared," says kvorc. "They had read that 'pirate sites' used it and that they're mining 'cryptocurrency'. "So, the users who didn't know better were shocked and scared and various antivirus programs screaming in agony with false positives didn't help either."
According to kvorc, the antivirus industry could also review what it sees as threats, claiming that although mining tools can be processor hungry, they are not significantly worse than many adverts that are not flagged. "It's funny how they don't flag flashy cookie ads as malware, but using CPU cycles that would otherwise be used by bad JavaScript in adverts is somehow dangerous," he says.
Changing tactics
JavaScript mining tools are evolving fast in response to concerns over performance and security software flagging the tools as malware - and the main players want to legitimise distributed mining.
CoinHive, for example, has released an updated version of its platform that can't be implemented without first gaining user permission, but the raw, no-consent- required version is still available on the site, albeit with a warning from the creators. "The miner itself does not come with a user interface - it's your responsibility to tell your users what's going on and to provide stats on mined hashes," the company says of the original miner in its FAQs. "While it's possible to run the miner without informing your users, we strongly advise against it. You know this."
Sound advice, but advice that can be easily ignored. "This thing is very new [and] there are no regulations, so platforms, sites and hackers are still trying to find a viable model for them. Inevitably they all make mistakes and learn," says Sinegubko. "As this thing matures there will be less room for abuse and it will be clearer what is acceptable use of this technology and what is not."
Image: Shutterstock




